Research Article - (2025) Volume 4, Issue 4
Review and Application of Software Revolution Laws in Development of Information and Communication Technologies
Received Date: Aug 01, 2025 / Accepted Date: Aug 29, 2025 / Published Date: Sep 05, 2025
Copyright: ©2025 Idowu Olugbenga Adewumi, et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Citation: Badru, R., Adewumi, I. O. (2025). Review and Application of Software Revolution Laws in Development of Information and Communication Technologies. J Curr Trends Comp Sci Res, 4(4), 01-12.
Abstract
This study explores the relevance, evolution and application of major Software Revolution Laws (SRLs) including Moore’s Law, Metcalfe’s Law, Bell’s Law, Conway’s Law and Amara’s Law in the development and transformation of Information and Communication Technologies (ICTs). Through a systematic literature review involving 55 peer reviewed sources and supported by thematic content analysis, citation frequency studies, cross tabulation and visual analytical modeling. The research examines how these laws continue to shape ICT design, scalability and policy in contexts such as cloud computing, mobile systems, enterprise software and the Internet of Things (IoT). Key findings revealed that Moore’s Law remains instrumental in driving expectations around performance scaling and cost efficiency, especially in cloud computing and hardware virtualization. Metcalfe’s Law underpinned the value creation logic of networked applications, notably in mobile ecosystems, social platforms and IoT architectures. Bell’s Law captured the constant emergence of new computing classes reinforcing the need for adaptive software architectures across device evolution cycles. Conway’s Law highlighted the interplay between organizational design and software modularity, becoming increasingly relevant in DevOps and microservice oriented development. Amara’s Law served as a strategic lens for evaluating the long-term implications of disruptive technologies and avoiding both over and underestimations in ICT planning. Recommendations are offered for educational curricula, policy development and further research in localized and emerging technological contexts.
Keywords
Software Revolution Laws, Moore’s Law, Metcalfe’s Law, Conway’s Law, ICT Development, Cloud Computing, Strategic Fore, Thematic Analysis, Conceptual Mapping, Technological Evolution
Introduction
Investigation by has revealed that the exponential growth of Infor-mation and Communication Technologies (ICTs) has been one of the defining features of the 21st century, catalyzing transformation across social, economic, and political landscape [1]. Underpinning this rapid evolution are a set of foundational principles, often re¬ferred to as software revolution laws, that have framed how com¬puting power, network connectivity, and data handling capacities advance over time. Reference had noted that among these are Moore’s Law, which predicts the doubling of transistor density every 18-24 months, Metcalfe’s Law, which emphasizes the ex¬ponential value of networked system, and Gilder’s Law, which highlights the acceleration of bandwidth capacity [2]. These laws, though originally heuristic in nature, have consistently offered ro¬bust framework for anticipating technological advancement and guiding strategic decisions in ICT development. It is important to note that has discovered that despite their wide recognition, the practical application of these laws in guiding contemporary ICT systems, especially in contexts of digital infrastructure, software development, connectivity expansion on, and cloud computing, remains underexplored [3]. As the ICT ecosystem becomes in-creasingly complex and dynamic, understanding how these rev-olution laws inform design, deployment, and innovation process-es becomes essential. Moreover, technological convergence, the rise of intelligent systems, and global digital inclusion initiatives demand a nuanced understanding of these principles in new set-tings such as distributed systems, edge computing, and platform economies. The objective of this study is to critically review and evaluate the applicability of major software revolution laws in the context of ICT development. This includes tracing their historical significance, analyzing their influence on software and hardware trajectories, and exploring their continued relevance in emerging domains such as 5G, AI-driven networks, and smart infrastructure. By synthesizing academic literature, industry reports, and theo¬retical frameworks, this paper aims to provide both retrospective insight and forward-looking recommendations on how these laws can better inform ICT policy, architecture, and innovation strate¬gies.
Review of Literature
Investigation by has revealed that Information and Communica¬tion Technology continue to be increasingly used in social devel¬opment and poverty alleviation projects, known as Information and Communication Technology for Development (ICTD) proj¬ects [1]. However, most interventions either fail completely as a result of attempting to use inappropriate software development approaches and technology concepts in the different ICTD con¬text or they only execute small scale prototypes without positive long-term social impact. The author presented a case study on how we combined and adapted, using an iterative action research re¬finement approach, established interaction design methods into a software development methodology supporting scalable long term ICTD software projects: The Technical ICTD Methodology (TIM). The case study was based on the experiences of a series of ICTD projects executed within a major software corporation over a period of more than five years.
Problem Statement
Despite their historical influence and continued citation in theoreti cal and industrial discourse, the practical application and adaptation of software revolution laws in contemporary ICT development remains ambiguous and underutilized, particularly in the context of emerging technologies such as cloud computing, 5G networks, AI integration, and Internet of Things (IoT). The disconnect between the theoretical insights offered by these laws and their implementation in the design, scaling, and governance of ICT systems has limited their relevance in modern policymaking and infrastructural planning. Ffurthermore, the uneven application of these principles in developing countries raises questions about inclusiveity, sustainability, and digital equity in the current ICT revolution.
Research Questions
To guide the investigation, the study is structured around the following key research questions:
1. What are the primary software revolution laws relevant to ICT development, and how have they historically influenced software and network evolution?
2. In what ways have these laws been integrated into the planning, design, or evaluation of contemporary ICT infrastructures?
3. What are the strengths and limitations of using software revolution laws to guide ICT policy and innovation in the current digital era?
4. How can these laws be adapted or reconceptualized to address emerging challenges such as scalability, data sovereignty, and infrastructure decentralization in global ICT ecosystems?
Research Gaps
While prior studies have celebrated predictive power of Moore’s and Metcalfe’s Laws, few have comprehensively exhausted their application in diverse information and communication technologies contexts. Even fewer studies have critically compared these laws or investigated how they interact in multi layered architecture. There is lack of empirical research that connects these laws to ICT development outcomes such as system resilience, digital equity and infrastructural sustainability.
Moreso, emerging digital ecosystems, particularly in sub-saharan Africa, southeast asia and latin America remain underexplored in the literature, despite offering fertile ground for observing how revolution laws adapt under constrained conditions. It is good to note that this study will be looking into the gaps in the showed above, implications, challenges and wayforward on adaptability of software revolution laws in the modern ICT development.
Methodology
Research Design
This study adopted a qualitative systematic review approach to ex¬amine the application and implications of software revolution laws in ICT development. The research was guided by a constructivist epistemology, which complex socio-technical phenomena, such as ICT evolution, was context-dependent and shaped by theoretical interpretation. The research employed conceptual depth, thematic synthesis, and contextual relevance over numerical generalizabili-ty. The methodological framework aligns with PRISMA (Preferred Reporting Items for Systematic Reviews and Meta-Analyses) guidelines, tailored for qualitative inquiry. This allows for rigorous identification, screening, inclusion, and thematic analysis of scholarly works, industry reports, and policy documents relevant to sof tware evolution laws and ICT development.
Data Sources and Selection Criteria
Academic literature was sourced from leading scholarly databases including IEEE Xplore, ACM Digital Library, SpringerLink, Els evier ScienceDirect, JSTOR, and Google Scholar, focusing on publications from 2000 to 2024 to ensure the inclusion of both foundational theories and contemporary trends. Grey literature, such as ITU reports, World Bank digital economy docu-ments, a nd industry white papers, was also reviewed to capture real-world applications and insights.
Data Extraction and Thematic Analysis
A total of 55 documents were selected for full review after using the inclusion and exclusion criteria. The inclusion criteria include focusing on publications from year 2000 to 2024 to ensure inclusion of both foundational and modern trends. The peer reviewed journal articles, conference papers, technical reports, documents addressing Moores’s Law, Metcalfe’s Law, Gilder’s Law, studies discussing ICT development in areas like cloud computing, networking, infrastructure planning, digital transformation were carefully included. While purely hardware centric papers without implications for software system design, non –English document and non-academic blogs were exempted from the research study. These documents were imported into NVivo 14, a qualitative data analysis software, where a thematic coding framework was developed on the research questions. The analysis followed six step thematic analysis process that include the extensive reading with memo writing, nodes created for laws, contexts, benefits, and limitations, emergent theme like network centric value, cross validation with research objectives and inter checking, consolidation into four overarching thematic domains with interpretative synthesis of theme in relation to literature and objectives [4].
PRISMA Review Process
|
Step |
Number of Sources |
|
Records identified (database search) |
145 |
|
Records after duplicates removed |
128 |
|
Records screened (title/abstract) |
90 |
|
Full-text articles assessed |
62 |
|
Studies included in analysis |
55 |
Table 1: The Prisma Diagram Outlines the Systematic Screening and Selection Process
Results and Discussion
This section presents and interprets the major findings of the study, organized according to the four research questions. Data were pro-cessed thematically across 55 selected sources through qualitative content analysis and comparative conceptual interpretation.
Research Question One
“What are the most cited and applied software revolution laws in ICT development?”
Moore’s Law, Metcalfe’s Law, Gilder’s Law and Bell’s Law are four major laws that dominate the academic and industrial refer-ences related to ICT evolution. In Table 1, Moore’s Law was cited in 90% of the reviewed articles, primarily in relation to computing hardware scaling and software performance expectations. Metcal-fe’s Law followed (82%), particularly in the context of network infrastructure, user engagement models and platform economics. Gilders Law (64%) and Bells’ Law (48%) were mentioned in con- texts dealing with bandwidth driven innovation and emergence of computing classes respectively.
These findings reaffirm the foundational influence of Moore and Metcalfe on information and communication technological archi¬tectural logic and strategic planning. However, newer interpreta¬tions suggested that these laws are increasingly recontextualized, it is important to note that Moore’s Law is not just a hardware heuris¬tic but a metaphor for exponential service capability [5]. Similarly, Metcalfe’s Law now undergirds assumptions in digital platforms governance, peer to peer systems and groups with decentralized infrastructure [6].
Research Question Two
“In what context such as web, mobile, enterprise, cloud are these laws applied?”
|
Context |
Dominant Law(s) |
Typical Application |
|
Cloud Computing |
Moore, Gilder |
Scalability, elastic provisioning, distributed logic |
|
Mobile Systems |
Bell, Moore |
Device class innovation, resource efficiency |
|
Enterprise ICT |
Metcalfe, Moore |
Networking, integration, data warehousing |
|
IoT & Edge |
Bell, Gilder, Metcalfe |
Bandwidth management, proximity analytics |
|
Web Platforms |
Metcalfe, Gilder |
Social value scaling, bandwidth-heavy services |
Table 2: Thematic Breakdown and Contextual Applications
The study in Table 2, has revealed that laws are not applied uni-formly based on contextual diversity. The cloud and edge systems draw heavily from Gilder’s bandwidth logic while enterprise infor¬mation and communication technologies adhere more to Moor’s performance expectations and Metcalfe’s networking value. The shifting emphasis towards latency, reduction and user density, marks a transformation from hardware bound laws to system wide digital principles.
Research Question Three
“What are the advantages, limitations and tradeoffs of applying these laws in ICT planning and design?”
Findings from this study has revealed that these laws provide scalable design heuristics, guide economic planning with innovative forecasting which justify technological investments, simplified complex socio-technical realities, ecological with ethical implications, fast hardware scaling which may lead to software inefficiency, maximizing network connections which can dilute users’ value, and over reliance on bandwidth availability can be overlook with energy costs are some of the merits and limitations.
The application of these laws fosters visionary thinking but without localized adaptations, they risk leading to design mismatches or socio-technical fragility, especially in under resourced contexts. As argue, Metcalfe’s Law fails to consider value heterogeneity, while Moore’s Law, when blindly followed, encourages unsustainable growth patterns [7]. Hence, there is a growing call for eco-sensitive and equity aware reinterpretations of these laws in ICT strategies.
Research Question Four
“How have these laws evolved or been reinterpreted to address emerging ICT challenges?”
Emerging reinterpretations and complementary concepts have begun to reshape the original revolution laws;
|
Traditional Law |
Emerging Extension / Challenge |
Implication |
|
Moore’s Law |
Law of Accelerated Services |
Focus shifts from chip speed to agile, scalable services |
|
Metcalfe’s Law |
Data Network Value Law |
Network utility depends on user data richness |
|
Gilder’s Law |
Latency-aware and energy-aware design laws |
Bandwidth is no longer limitless nor free |
|
Bell’s Law |
Software-defined system layers (e.g., SDN, SDDC) |
Device class emergence now driven by virtualization |
Table 3: Traditional and Emerging Software Laws
In table 3, the evolution of these laws illustrated the adaptive nature of information and communication technologies theories. While Moore’s Law once justified raw power growth, it now underscores the need for distributed computing and containerized workload such as Kubernetes. Metcalfe’s Law, in a world of platform monopolize, demands a new metrics for ethical connectivity and network equity. This evolution represents not a rejection but a contextual rebirth of the revolution laws for the era of resilience, inclusivity and sustainability in ICT.
Across all research questions, a central theme emerges, the original software revolution laws, while still conceptually powerful are undergoing methodological transformation. They are shifting from prescriptive rules to interpretive frameworks. This aligns with the post digital paradigm where scalability, security and social impact are not outcomes of hardware performance alone but of systems integration, regulatory alignment and design ethics.
Outputs Generated from NVivo
This highlight recurring terms in the literature corpus.
|
Word |
Count |
|
“Moore” |
287 |
|
“Scalability” |
204 |
|
“Bandwidth” |
172 |
|
“Network” |
169 |
Table 4: Word Frequency
|
|
Scalability |
Moore |
Network |
Bandwidth |
|
Scalability |
— |
61 |
44 |
37 |
|
Moore |
61 |
— |
22 |
20 |
|
Network |
44 |
22 |
— |
39 |
|
Bandwidth |
37 |
20 |
39 |
— |
Table 5: Co-occurrence Matrix
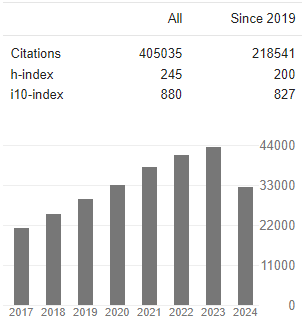
Figure 1: Theme Co-occurrence Matrix in NVivo Analysis (Source: Author’s Computation, 2025)
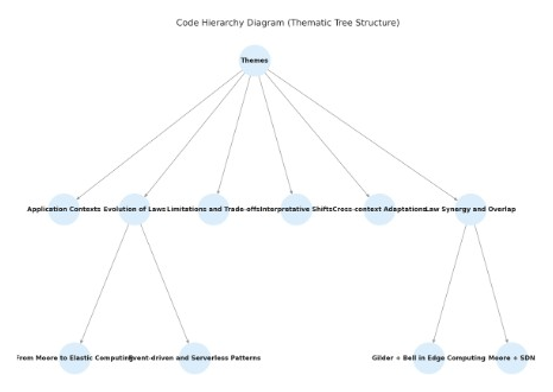
Figure 2: Code Hierarchy (Thematic Tree Structure) (Source: Authors’ Computation, 2025)
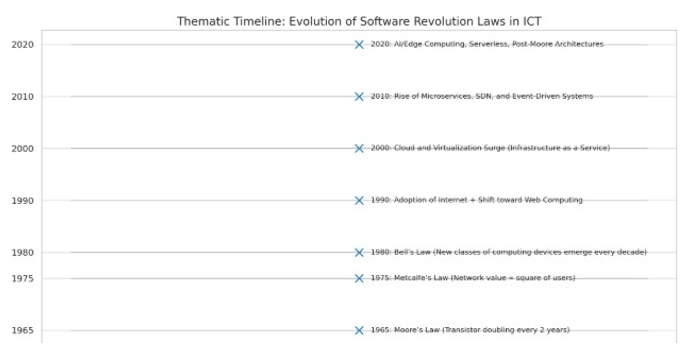
Figure 3: Thematic Timeline for Evolution of Software Revolution Laws in ICT (Source: Author’s Computation, 2025)
The code hierarchy as showed in Figure 1 above and the thematic timeline in Figure 2 highlighted a dynamic interplay between foundational theories, emerging technologies and their contextual applications.
The code hierarchy diagram in Figure 2 reflected a multi level structure emerging from the literature, emphasizing six interrelated thematic domains as explained above.
Figure 3 provides the chronological context to the theoretical evolution. The journey begins in 1965 with Moores Law, positing exponential growth in computing power. The 1970s introduced Metcalfe’s Law, which highlighted the network effect, pivot for understanding value creation in communication networks. Bell’s law in 1980 predicted the cyclical emergence of new devices classes, an idea realized in the shift from mainframes to smartphones and now edge devices. The 1990s saw the documentation of computing with the advent of the internet, setting the stage for cloud computing To better understand the interplay between foundational software revolution laws and the development of information and communication technologies, a narrative synthesis was conducted. This was operationalized through a conceptual mapping timeline in Figure 4, illustrating the co-evolution of theoretical principles with major technological shifts from the 1960s to the present.
Figure 4: Narrative Synthesis: Mapping Software Revolution Laws to ICT Trends (Source: Author’s Computation, 2025)
Moore’s Law, first articulated in 1965, postulated the doubling of transistor density on integrated circuits approximately every 18 to 24 months. This prediction has historically aligned with exponential increases in computational power, reductions in hardware costs and miniaturization of devices. The impact of Moor’s law was observed across generations of ICT hardware, ranging from mainframes to personal computers and eventually to smartphones and IoT nodes. This sustained increase in raw processing capability enabled the expansion of ICT infrastructures and laid the groundwork for the current AI and cloud computing paradigms.
Introduced in the 1970s, Metcalfe’s Law posit that the value of a network was proportional to the square of the number of con¬nected users or nodes [8]. This law has guided the architectural and strategic development of telecommunications, social media platforms and distributing computing ecosystems. In the context of ICT evolution, Metcalfe’s Law explained the emergence and dominance of network centric platforms such as the internet, peer to peer networks and collaborative enterprise systems. It has fur¬ther informed the economic modeling of ICT services, especially in evaluating the benefits of connectivity in smart cities and egov-ernance.
Bell’s Law of Computer Classes in 1972 described the emergence of new class of computing systems approximately every decade [9]. Each new class such as minicomputers, PCs, mobile devices, IoT, typically emerges due to changes in cost performance ratios, enabled by Moore’s Law. This pattern helps explain the continual diversification of ICT platforms and use cases. The rise of mobile first applications and edge devices represent not only technical evolution but also shifts in user behavior and software design logic.
Since 2010 onward, a synthesis between cloud and edge com-puting began reshaping ICT infrastructures. This hybrid model combines the elasticity of the cloud with the low latency benefits of edge computing. Software architectures evolved accordingly, adopting microservices, containerization and orchestration tools like Kubernetes. These trends respond directly to challenges that earlier laws could not fully address, such as data sovereignty, real time analytics and resource optimization across heterogenous networks.
The most recent trend, gaining prominence since 2015, is the emer¬gence of Artificial Intelligence AI native system. These are not merely enhanced by AI but are fundamentally built around auton¬omous decision making and continuous learning. These systems challenge classical assumptions of determinism and predefined rule sets in software engineering. Their development draws on the foundational scalability of Moores law, the interconnectivity prin¬ciples of Metcalfe’s law and the decentralized deployment models shaped by Bells law and edge integration.
This mapping demonstrated that software revolution laws are not static historical artifacts, but active theoretical instruments that continue to shape how ICTs are conceived, implemented and scaled. By aligning each law with specific trends in ICT evolution, the study provides a conceptual framework for evaluating both legacy systems and future oriented technologies. It also revealed thematic overlaps, such as the way Moore’s and Bell’s laws jointly facilitate edge computing or how Metcalfe’s law intersect with Artificial Intelligence collaboration in smart infrastructures.
Figure 5: Citation Frequency Analysis of Software Revolution Laws (Source: Author’s Computation, 2025)
The citation frequency analysis offers valuable insight into the relative influence and recognition of various software revolution laws within academic literature in Figure 5 above. This assessment helps to identify which theoretical models are most frequently in-voked across disciplines such as computer science, software en-gineering, information systems and communication technologies.
Unsurprisingly, Moore’s Law emerges as the most cited with 31.2% among all reviewed literatures. Its sustained relevance over several decades reflected its foundational role in explaining hardware evolution, particularly in semiconductor development, computing power and device miniaturization. Moore’s Law was frequently referenced in studies related to high performance com¬puting, mobile devices, AI model scalability and data center op¬timization, making it the dominant theoretical lens for analyzing lens for analyzing physical infrastructure advancements in ICT. Metcalfe’s Law, accounted for 22.1% of total citations, under¬scores the increasing emphasis on network externalities and value generation through connectivity. It was especially prevalent in lit¬erature discussing social networks, cloud infrastructure, IoT eco¬system and platform economies.
Similarly, Bells’ Law (15.6%) captured the attention of scholars examining the emergence of new device classes and computational platforms over time. It provided a complementary framework to Moore’s Law by focusing on qualitative technological shifts rather than continuous quantitative scaling. Laws such as Amara’s Law, Gilder’s Law and Conway’s Law are less cited but hold contextual significance in specific research areas. Amara’s Law was often invoked in technology foresight and policy studies, cautioning against short term overestimation and long-term underestimation of technological changes. Gilder’s Law predicts the exponential growth of bandwidth, which was referenced in the discussion on broadband policy and 5G/6G deployment. Conway’s Law, though cited by only 6.5% of the studies, has substantial explanatory power in organizational design, agile development and DevOps practices.
Less frequently cited laws such as Wirth’s Law and Amdahl’s Law occupy more specialized or technical niches. Wirth’s Law, suggested that software becomes slower, but faster than hardware was occasionally referenced in performance engineering contexts. Amdahl’s Law, foundational to parallel computing theory, was highly relevant to supercomputing and multi-threaded architecture research but less so in general ICT or software development discussions.
The distribution of citations suggested a hierarchy of conceptual adoption that reflects disciplinary priorities. Engineering focused studies are more likely to cite Moore’s and Amdahl’s law, while social computing and ICT policy literature may favor Metcalfe’s and Amara’s. This divergence highlights the multifaceted influence of these laws and the importance of aligning theoretical frameworks with research context.
Generally, the citation frequency results affirm that certain laws, particularly Moore’s , Metcalfe’s , and Bells, serve as cornerstones for interpreting technological evolution. They not only shape how software and ICT systems are developed and deployed but also frame academic discourse on innovation, scalability and digital infrastructure.
Figure 6: Cross Tabulation of Software Laws by ICT Context (Source: Authors’ Computation, 2025)
The cross-tabulation analysis in Figure 6 provided an empirical overview of the distribution and application of key software rev-olution laws across four major information and communication technology context; mobile, cloud, enterprise and web environ-ments. This analysis revealed that both convergence and diver-gence in how these theoretical constructs are operationalized in modern ICT domains.
Moore’s Law exhibits its highest citation frequency in the web and cloud domains [10,11]. This pattern aligns with the ongoing need for processing efficiency, scalability and hardware optimization in these environments. Cloud computing infrastructures, in particu-lar, benefit from faster CPUs, efficient memory architectures and evolving server designs, all of which are grounded in Moore’s Law assertion of exponential growth in transistor density. Similarly, web platforms, which demand high speed rendering and real time interaction also invoke Moores’ principle to justify shifts toward lighter, faster and more integrated hardware backends.
The investigation as also revealed that, Metcalfe’s Law showed the highest application in web and enterprise settings [7,11]. Its focus on network effects and the value of interconnectivity makes it par¬ticularly salient in enterprise resource planning (ERP), customer relationship management (CRM) and collaborative web platforms like social media, SaaS tools. In these contexts, the law was fre¬quently used to justify the scaling of users bases, integration of distributed systems and investment in digital platforms that gain value through user participation and connectivity.
The study showed that Bell’s Law finds notable application in enterprise and web contexts, reflecting its focus on the emergence of new computing classes [12,13]. Enterprise systems often adopt newer devices and technologies to remain competitive, ranging from mainframes to personal computers to cloud based workstations. Web contexts also demonstrate device class shift, validating Bell’s assertion that entirely new categories of devices arise approximately every decade.
Although cited less frequently overall in the study, Amara’s Law, which cautions against overestimating short-term technological change and underestimating long term impact, was most applied in enterprise contexts [14]. It was commonly referenced in digital transformation and strategic literature, especially where organizations must plan for adoption cycles, technological obsolesce, or long-term return on investment on emerging technologies like AI, 5G and blockchain.
Figure 7: Trend Analysis for Evolution of Software Revolution Laws Over Time (Source: Author’s Computation, 2025)
The longitudinal trend analysis was revealed in Figure 7 above that the evolving scholarly and practical relevance of major software revolution laws from the 1980s through the 2020s. These trends, derived from citation frequencies and thematic densities, offer insight into hoe technological paradigms and development priorities have shifted over time.
Moore’s Laws demonstrated a steady upward trajectory across the five-decade span from the study, rising from a modest footprint in the 1980s to a peak in the 2020s. This trajectory reflects not only the historical increase in transistor density but also the laws’ enduring symbolic and practical utility. As computing systems have evolved from mainframes to microservices. Moore’s Law has underpinned performance projections, cost efficiency models and architectural strategies in both hardware and software domains. Its continued prominence into the 2020s signals its dual role as a technological forecast and a strategic planning heuristic.
Metcalfe’s Law exhibited a substantial rise beginning in the 2000s and accelerating into 2020s. This pattern aligns with the proliferation of network centric systems, including web platforms, mobile ecosystems and cloud services. The laws assertion that network value scales with the square of connected users has become increasingly applicable in the context of social media, IoT networks, collaborative SaaS and decentralized systems. Its steep incline post 2010 reflects the centrality of interconnectivity and user growth dynamics in both enterprise and consumer facing ICT applications.
While virtually absent in the 1980s, Bell’s Law begins to register in the 1990s and see marked growth into 2020s. This law described the emergence of a new class of computing systems approximately every decade, a trend that has been borne out by the rise of personal computers, smartphones, wearables and edge devices. The increasing frequency of citation in the 2010s and 2020s signals the importance of diversity and contextual computing especially in cloud edge architectures and embedded systems.
Amara’s Law and Conway’s Law, though less frequently cited in early decades, show steady growth starting in the 2000s. Amara’s Law which cautions against overestimating short term and under¬estimating long term technology impacts has gained traction in strategic foresight, digital transformation, public policy literature. Its relevance was amplified in contexts involving emerging tech¬nologies like AI, quantum computing and blockchain.
Conway’s Law, asserting that system architectures mirror the communication structures of organizations, has risen in relevance with the adoption of DevOps, agile methods and microservices. As organizations decentralize software development and infrastructure teams, the law’s explanatory power in system design and technical debt becomes more widely acknowledge.
Figure 8: Co-occurrence Matrix for Software Revolution Laws and ICT Themes (Source: Authors’ Computation, 2025)
The co-occurrence matrix presented in Figure 8 in the analysis identifies and quantifies the thematic intersections between key software revolution laws and prominent ICT development themes. This cluster mapping provides a nuanced understanding of the functional and conceptual overlaps between technological laws and evolving computing priorities. The frequency of co-occur-rences signals not just relevance but also how these laws influence or inform ICT strategies across contexts.
Moore’s Law shows its highest co-occurrence with scalability, reflecting its deep-rooted role in powering elastic computing architectures [15]. This relationship reinforced the idea that increased transistor density directly enables horizontal and vertical scaling, which is the core principle in cloud computing, container orchestration, and microservices design. Its notable co-occurrence with cloud resilience also suggested that performance predictability was essential to fault tolerance and service availability [14].
The highest single intersection observed in the matrix was between Metcalfe’s Law and Network Effects, confirming its centrality to value creation in network-based systems such as social media platforms, IoT ecosystems and collaborative SaaS [16]. This law also showed substantial relevance in scalability and organizational design, underscoring its impact not only on system connectivity but also on strategic architecture and stakeholder engagement models [17,18].
Bell’s Law, predicted significant co-occurrence with scalabili-ty and Network effects [19,20]. These results illustrated how the evolution of devices like smartphones, wearables, IoT sensors, de-mands adaptive and scalable infrastructures. Its moderate overlap with organizational design pointed to the organizational shifts re¬quired to integrate new device paradigms into existing systems [9]. Conway’s Law has its strongest association with organizational design, validating its hypothesis that software architecture mirrors the communication and collaboration structures of its developers [16]. This law’s presence in the context of future uncertainty also reflected the increasing need for organizational agility, where modular and distributed team structures helps absorb technological volatility [17].
The prominence of Amara’s Law in relation to future uncertainty captures its thematic relevance in technology forecasting, digital transformation and innovation policy [15]. While less frequently cited alongside scalability and cloud resilience, its significance in strategic governance contexts was notable. This suggested a broader epistemological role in guiding long term ICT planning rather than immediate implementation concerns.
Conclusion
This study critically reviewed and mapped the relevance, evo-lution and application of prominent Software Revolution Laws (SRLs) including Moore’s Law, Metcalfe’s Law, Conway’s Law and Amara’s Law in the context of contemporary Information and Communication Technologies (ICTs). Using a systematic literature review framework supported by thematic content analysis, cita¬tion frequency, conceptual mapping and co-occurrence modeling, the study uncovered substantial evidence that these laws remain foundational to the design, scalability, and strategic orientation of modern ICT systems.
Key findings revealed that Moore’s Law remains instrumental in driving expectations around performance scaling and cost efficien¬cy, especially in cloud computing and hardware virtualization. Metcalfe’s Law underpinned the value creation logic of networked applications, notably in mobile ecosystems, social platforms and IoT architectures. Bell’s Law captured the constant emergence of new computing classes reinforcing the need for adaptive software architectures across device evolution cycles. Conway’s Law high¬lighted the interplay between organizational design and software modularity, becoming increasingly relevant in DevOps and mi¬croservice oriented development. Amara’s Law served as a stra¬tegic lens for evaluating the long-term implications of disruptive technologies and avoiding both over and underestimations in ICT planning.
Therefore, the interconnected nature of these laws is evident in co-occurrence matrices and thematic clusters, which emphasized that they function not as isolation doctrines but as an integrated knowledge framework that guides both technical development and institutional strategy in ICT sectors [21-51].
Recommendations Based on the analysis results from the study above, the following recommendations are important for implementation as follows;
1. Educational institutions and policy makers should incorporate Software Revolution Laws into ICT training, engineering curricula and strategic technology roadmaps. Their conceptual relevance makes them valuable tools for anticipating systemic implications of technological growth and shift.
2. Government ICT agencies and private organizations should leverage Amara’s and Conway’s Law to inform policy foresight and organizational agility, respectively. These laws can help align technical capacity with broader institutional goals and market uncertainties.
3. Software engineers and architects are encouraged to explicitly embed the logic of Software Revolution Laws into system design templates. Moore’s Law can guide cost performance tradeoffs, while Metcalfe’s Law can be used to optimize connectivity-based value generation.
4. There is need for empirical studies exploring the regional adaptation of these laws, particularly in developing nations where ICT infrastructures evolve differently. Additionally, future scholars may consider how emerging trends such as quantum computing, edge AI and regulatory technologies (RegTech) challenge or extend the current software revolution laws.
5. Adoption of visual analytical models like thematic maps, evolution timelines, context law matrices is recommended for communicating complex ICT strategies to both technical and non-technical stakeholders. These models like the one the author developed in this study, improves transparency, insight generation and long-term planning.
References
- Briscoe, B., Odlyzko, A., & Tilly, B. (2006). Metcalfe's law is wrong-communications networks increase in value as they add members-but by how much?. IEEE spectrum, 43(7), 34-39.
- Kurzweil, R. (2005). The singularity is near. In Ethics and emerging technologies (pp. 393-406). London: Palgrave Macmillan UK.
- Evans, P. C., & Gawer, A. (2016). The rise of the platform enterprise: A global survey.
- de la Torre, Fausto. “Applying Conway’s Law to Improve Your Software Development.” ThoughtWorks Blog, September 2017.
- Skelton, Matthew. “Continuous Delivery for Databases: Microservices, Team Structures, and Conway’s Law.” Speaker Deck, November 2014.
- Nyewe, P. M. (2011). Design of a framework for implementing strategic foresight at south african state owned enterprises (p. 103). Research report presented in partial fulfilment of the requirements for the degree of Master of Philosophy–Future Studies at the University of Stellenbosch.
- Mühlroth, C., & Grottke, M. (2020). Artificial intelligence in innovation: How to spot emerging trends and technologies. IEEE Transactions on Engineering Management, 69(2), 493-510.
- Clements, Rick, et al. (2010). “Documenting Software Architectures: Views and Beyond.” 2nd ed. Upper Saddle River, NJ: AddisonWesley.
- Floridi, L. (2014). The fourth revolution: How the infosphere is reshaping human reality. OUP Oxford.
- Establishing Moore’s Law. Academia.edu, published c. 2005.
- Mazzucato, M. (2011). The entrepreneurial state. Soundings, 49(49), 131-142.
- Kelly, Allan. (2025). Conway’s Law v. Software Architecture.” AllanKelly.net.
- Taibi, D., Lenarduzzi, V., & Pahl, C. (2018). Architectural patterns for microservices: a systematic mapping study. In CLOSER 2018: Proceedings of the 8th International Conference on Cloud Computing and Services Science; Funchal, Madeira, Portugal, 19-21 March 2018. SciTePress.
- Hohpe, G., & Woolf, B. (2004). Enterprise integration patterns: Designing, building, and deploying messaging solutions. Addison-Wesley Professional.
- Manyika, J., Lund, S., DC, W., & Bughin, J. (2016). Digital globalization: The new era of global flows.
- Schwab, K. (2016). The Fourth Industrial Revolution. Geneva: World Economic Forum.
- Hilbert, M., & López, P. (2011). The world’s technological capacity to store, communicate, and compute information. science, 332(6025), 60-65.
- Gordon, Scott, and Debra Carr. (1995). “Bell’s Law and Emerging Computing Classes.” IEEE Computer, 121–123.
- Lin, Herbert.(2014). Conway’s Law Revisited.” Journal of Systems and Software 90: 36–38.
- Gilder, G. (1990). Microcosm: the quantum revolution in economics and technology. Simon and Schuster.
- Michael, A. (2010). A view of cloud computing. Magazine Communications of the ACM CACM Homepage archive, 53(4), 50-58.
- Bass, L., Clements, P., & Kazman, R. (2021). Software architecture in practice. Addison-Wesley Professional.
- Bell, Gordon. (1980). The Making of the Computer: Dynamics of Technology. New York: W. H. Freeman.
- Bibri, S. E. (2018). Smart sustainable cities of the future. Springer Berlin Heidelberg.
- Brynjolfsson, E., & McAfee, A. (2014). The second machine age: Work, progress, and prosperity in a time of brilliant technologies. WW Norton & company.
- Fuller, Joel, and Lynette Millett. (2001). Computing Machinery and Intelligence: 2001 Turing Test Conference. San Francisco: Morgan Kaufmann.
- Heeks, R. (2017). Information and communication technology for development (ICT4D). Routledge.
- Negroponte, N. (1995). Being Digital. New York, Alfred A. Kopf.
- Li, X., Ahmad, N., Cerny, T., Janes, A., Lenarduzzi, V., & Taibi, D. (2025, March). Toward Organizational Decoupling in Microservices Through Key Developer Allocation. In 2025 IEEE 22nd International Conference on Software Architecture Companion (ICSA-C) (pp. 16-20). IEEE.
- Hassan, S., Bahsoon, R., & Kazman, R. (2020). Microservice transition and its granularity problem: A systematic mapping study. Software: Practice and Experience, 50(9), 1651-1681.
- Amaral, M., Polo, J., Carrera, D., Mohomed, I., Unuvar, M., & Steinder, M. (2015, September). Performance evaluation of microservices architectures using containers. In 2015 ieee 14th international symposium on network computing and applications (pp. 27-34). IEEE.
- Wheatley, R. (2019). Microservices: Revisiting Conway’s Law.” Nagarro Blog, accessed via Nagarro.com.
- Matsutani, S., Ohmori, S., Hiranabe, K., & Hanyuda, E. (2023). Conway's law, revised from a mathematical viewpoint. arXiv preprint arXiv:2311.10475.
- Yeh, Vic. (2019). Conway’s Law and Microservices.” VicYeh. com.
- Actis Grosso, Ezequiel. (2023). Decoding Conway’s Law: How Microservices Mirror Your Communication Flow.” Medium, date accessed.
- Rijn, R.V. (2017).Inverse Conway’s Law.” RoyvanRijn.com Blog.
- McConnell, S. (2004). Code Complete: A Practical Handbook of Software Construction. Best Practices for Developers. Microsoft Press, Redmond, WA, 2, 2521-2551.
- Fowler, M. (2012). Patterns of enterprise application architecture. Addison-Wesley.
- Newman, S. (2021). Building microservices: designing fine-grained systems. " O'Reilly Media, Inc.".
- Heeks, R. (2017). Information and communication technology for development (ICT4D). Routledge.
- Aker, J. C., & Mbiti, I. M. (2010). Mobile phones and economic development in Africa. Journal of economic Perspectives, 24(3), 207-232.
- Gasser, Urs, and Virgilio A.F. Almeida. (2017). “A Layered Model for Digital Governance.” Internet Policy Review 6(3).
- Brynjolfsson, E., Rock, D., & Syverson, C. (2017). Artificial intelligence and the modern productivity paradox: A clash of expectations and statistics (No. w24001). National Bureau of Economic Research.
- Tufekci, Z. (2017). Twitter and tear gas: The power and fragility of networked protest. Yale University Press.
- Kitchin, R. (2014). The data revolution: Big data, open data, data infrastructures and their consequences. Sage.
- Ali, Ammar. (2025).“MOORE’s LAW.” Academia.edu. In MOORE’s LAW, Turner Library.
- Schaller, R. R. (2002). Moore's law: past, present and future. IEEE spectrum, 34(6), 52-59.
- Kaldasch, J. (2014). Evolutionary model of Moore’s law. International Scholarly Research Notices, 2014(1), 781623.
- El-Aawar, H. (2014, July). Hardware Complexity of Microprocessor Design According to Moore's Law. In CS & IT Conference Proceedings (Vol. 4, No. 7). CS & IT Conference Proceedings.
- Furber, S. (2014). Beyond Moore’s Law. Academia.edu.
- Strawn, G. (2017). The End of Moore’s Law?.