Review Article - (2025) Volume 3, Issue 3
Quantum Social Engineering: A New Threat Paradigm in Cybersecurity
Received Date: Apr 14, 2025 / Accepted Date: Apr 30, 2025 / Published Date: Jun 10, 2025
Copyright: ©©2025 Maharshi Patel. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Citation: Patel, M. (2025). Quantum Social Engineering: A New Threat Paradigm in Cybersecurity. Int J Med Net, 3(3), 01-09.
Abstract
The advent of quantum computing is set to disrupt the very foundations of modern cybersecurity, rendering traditional encryption techniques vulnerable. A particularly alarming consequence of this revolution is the rise of Quantum Social Engineering, where quantum capabilities are harnessed to amplify and enhance conventional social engineering attacks. This paper explores the potential risks posed by quantum technologies in the realm of social engineering, focusing on how quantum computing can break current security mechanisms and exploit human weaknesses. By examining how quantum-powered attacks can enhance phishing, identity theft, and impersonation strategies, the paper identifies the critical need for quantum-resistant cryptographic systems, Quantum Key Distribution (QKD), and human-centered security protocols [1]. The study concludes by offering potential solutions to mitigate the emerging threats posed by Quantum Social Engineering, emphasizing the importance of preparing cybersecurity strategies for a post-quantum world.
Keywords
Quantum Social Engineering, Quantum-Aware Cybersecurity, Post-Quantum Cryptography (PQC), Quantum Key Distribution (QKD) and Quantum-Resistant Encryption
Introduction
In the ever-evolving landscape of cybersecurity, the emergence of quantum computing promises to revolutionize the way we approach data protection and threat mitigation. However, this groundbreaking technology also introduces a new dimension of vulnerability—one that extends beyond traditional cryptographic defenses [2]. While much of the discourse surrounding quantum, computing focuses on its potential to crack existing encryption algorithms, an often overlooked threat is its ability to amplify social engineering attacks. Enter the realm of Quantum Social Engineering, a hybrid threat model that combines the psychological manipulation inherent in social engineering with the computational power of quantum systems.
Traditional social engineering tactics rely on exploiting human psychology, often bypassing even the most sophisticated security protocols. Whether through phishing emails, pretexting, or impersonation, attackers deceive individuals into divulging sensitive information or performing actions that compromise security [3]. Quantum computing, with its ability to process vast amounts of data and break encryption at unprecedented speeds, presents a new and terrifying possibility: attackers could not only manipulate individuals but also decrypt private communications, forge identities, and spoof digital signatures with ease.
This paper delves into the fusion of quantum computing and social engineering, a convergence that could redefine the future of cybercrime[4]. While quantum computers have the potential to disrupt existing cryptographic frameworks, the intersection of these capabilities with human vulnerabilities presents an even greater risk [5]. The use of quantum enhanced phishing, identity theft, and deep fake impersonations could drastically elevate the sophistication and effectiveness of social engineering tactics. As these technologies evolve, cybersecurity strategies must adapt to address threats that are no longer merely technological but also deeply psychological.
This research explores the emerging threat of Quantum Social Engineering, outlines its potential implications for cybersecurity, and proposes strategies to defend against this new breed of attacks [5]. Through the integration of quantum-resistant cryptography, quantum key distribution, and human-centric security measures, this paper aims to offer a comprehensive framework for combating the growing risk of quantum-powered cyber threats.
Quantum-Enhanced Social Engineering
• Phishing Attacks in the Quantum Era
Phishing, one of the most common social engineering tactics, preys on human trust to extract sensitive information such as passwords, financial details, and personal credentials. Attackers typically use deception to impersonate trusted entities, often in the form of emails, websites, or phone calls that appear legitimate. The goal is simple: lure the target into revealing confidential data, which is then exploited for malicious purposes.
However, the advent of quantum computing introduces a new layer of complexity to this already dangerous cyber threat. Quantum computers have the theoretical ability to break widely used encryption schemes that currently protect digital communications [6]. Algorithms like RSA, which rely on the difficulty of factoring large numbers, could be easily decrypted by a sufficiently powerful quantum machine using Shor’s algorithm. This ability could be exploited by attackers in phishing attacks, where the legitimacy of digital communications—often protected by encryption—could be compromised.
With quantum-enhanced decryption capabilities, attackers could gain access to private emails, secure communications, and financial transactions. This would allow them to spoof digital signatures, forge secure messages, and gain unauthorized access to accounts [7]. For instance, an attacker could intercept an encrypted message from a legitimate entity and use quantum computing to decrypt it in real-time, exposing sensitive information [8]. Armed with this capability, they could easily impersonate the sender, modifying the message or directing the victim to a fake website. The ability to bypass encryption would make the usual phishing defense mechanisms—such as checking for SSL certificates or verifying the authenticity of a domain— obsolete.
Moreover, quantum computing’s influence on public key infrastructures (PKI), which underpin digital signatures and secure communications, could drastically reduce the security posture of online platforms. The ease of quantum decryption would enable cybercriminals to engage in advanced phishing schemes—from more sophisticated fake websites to fraudulent emails—leading to higher success rates and greater financial and reputational damage to the targeted individuals and organizations.
• Fabricating Digital Identities
One of the more concerning threats posed by quantum computing lies in its potential to bypass existing identity verification systems, which rely heavily on encryption to protect sensitive personal data [9]. In today’s digital world, identity management systems utilize encryption algorithms to safeguard passwords, biometric data, and other personal credentials. These systems typically depend on cryptographic methods such as hashing and public- key cryptography to protect identities in databases, ensuring that unauthorized access remains impossible [10].
Quantum computers, however, could potentially break these cryptographic systems, rendering them obsolete. Using Shor’s algorithm, quantum machines could factor large numbers and solve problems considered impossible for classical computers. This would enable quantum-powered attackers to break into systems that store encrypted credentials—whether through compromising passwords or bypassing encryption entirely. Once these credentials are decrypted, attackers would have access to a range of sensitive data, including Social Security numbers, bank account details, and biometric data [11].
The implications of this capability are profound. Digital identity theft could escalate to new levels of sophistication, as attackers could easily forge fake identities or impersonate individuals online. Traditional methods of identity verification, such as passwords, PINs, and even biometric authentication (e.g., fingerprints or facial recognition), would be vulnerable to quantum attacks. For instance, an attacker with access to quantum computing resources could bypass identity checks at banks, e-commerce platforms, or government services, effectively stealing someone's identity in a matter of seconds.
In practical terms, this would lead to widespread identity fraud, where criminals impersonate legitimate individuals to open fraudulent accounts, transfer funds, or access private services. Reputational damage, financial loss, and legal consequences could follow for both individuals and organizations affected by these quantum-enhanced identity theft schemes.
To mitigate these risks, it would be crucial to invest in postquantum cryptography (PQC) solutions, which offer quantum-resistant algorithms capable of withstanding the decryption powers of quantum computers. Until such systems are in place, the integrity of digital identity verification systems will remain highly susceptible to quantum-powered attacks.
• Exploiting Deep Fake Technologies
In recent years, deep fake technology has become an alarming tool for cybercriminals, enabling the creation of highly realistic audio and video impersonations of individuals. By utilizing artificial intelligence (AI) and machine learning algorithms, deep fakes can synthesize convincing representations of a person’s likeness, voice, and mannerisms, often making it difficult to distinguish between a genuine and fabricated source [12]. While the technology itself is impressive, it also poses serious risks to cybersecurity, particularly in the realm of social engineering.
Quantum computing, with its immense computational power, could exponentially enhance the capabilities of AI-driven deep fake technologies. Quantum-enhanced AI systems would be able to generate even more convincing impersonations by processing and analyzing far larger datasets at higher speeds than current classical computers. This amplification of deep fake technology would make it even more challenging for individuals to differentiate between authentic and malicious content, increasing the success rate of social engineering attacks.
For instance, attackers could create deep fake videos of executives or trusted figures, using quantum computing to generate highly accurate voice models or facial features. These fake videos could be used in targeted spear-phishing attacks, where a victim is tricked into transferring funds, disclosing sensitive information, or performing unauthorized actions based on an apparent direct request from their boss or colleague [13]. Similarly, audio deep fakes could mimic a trusted individual’s voice, prompting the victim to act based on fabricated instructions. The realism of these impersonations would make them incredibly effective at deceiving both employees and customers, leading to financial losses, data breaches, and other forms of cybercrime.
Furthermore, quantum computing could assist in the generation of deep fake content at scale, allowing attackers to target multiple victims simultaneously, thereby increasing the scope of the attack. The ability to produce personalized, convincing deep fakes tailored to specific targets could exponentially raise the stakes for both individuals and organizations. It’s possible that these quantum- enhanced deep fakes could also bypass current fraud detection systems used by law enforcement or financial institutions, making it harder to trace the perpetrators and prevent further damage.
To counter this, advancements in deep fake detection algorithms and quantum-resistant security protocols will be necessary to safeguard against the growing threat. Governments, corporations, and individuals alike will need to stay ahead of these evolving threats by adopting multifactor authentication systems and investing in AI-powered fraud detection tools capable of identifying deep fake content.
This detailed exploration of Quantum-Enhanced Social Engineering provides a comprehensive understanding of the heightened threats posed by quantum computing in the realms of phishing, identity theft, and deep fakes. The increasing sophistication of these attacks calls for new strategies, including the integration of quantum- resistant technologies and AI-driven security measures, to protect against the rising tide of quantum-powered cybercrime.
Mitigating Quantum Social Engineering Threats
• Post-Quantum Cryptography (PQC)
As quantum computing advances, it promises to revolutionize many industries, but it also poses significant risks to our digital infrastructure, particularly when it comes to data security. Traditional cryptographic systems that protect everything from online banking transactions to personal communications could be easily compromised by the power of quantum computers. Classical encryption methods, such as RSA and Elliptic Curve Cryptography (ECC), rely on mathematical problems (like factoring large numbers and solving discrete logarithms) that quantum algorithms, notably Shor’s algorithm, could solve exponentially faster than classical machines [14]. This means that encryption systems widely used today would be vulnerable to quantum attacks, potentially leading to widespread breaches of sensitive information.
To combat this looming threat, the development of Postquantum Cryptography (PQC) has emerged as a critical area of research. PQC involves designing cryptographic algorithms that are resistant to attacks by quantum computers. These new algorithms must be robust enough to withstand the computational power of quantum machines while remaining efficient for real-world applications.
One promising family of PQC techniques is lattice-based cryptography, which relies on complex mathematical structures called lattices to secure data [15]. These systems are believed to be resistant to quantum attacks because the problems they are based on (such as finding short vectors in high-dimensional spaces) are difficult to solve even for quantum computers. Hash- based signatures are another approach, using cryptographic hash functions to ensure data integrity, while multivariate polynomial cryptography focuses on solving systems of polynomial equations—a task that remains computationally hard for quantum algorithms.
|
Cryptogra phic Algorithm |
Classical Security |
Quantum Security |
Post- Quantum Algorithm |
Resistance to Quantum Attacks |
|
RSA |
Breakable by Quantum |
Breakable by Quantum |
Lattice- Based Cryptograph y |
High |
|
ECC |
Breakable by Quantum |
Breakable by Quantum |
Multivariate Polynomial |
High |
|
AES |
Secure |
Breakable by Shor’s Algorithm |
Hash-Based Signatures |
Moderate |
Table 1: Comparison of Classical, Quantum, and Postquantum Cryptographic Algorithms [16]
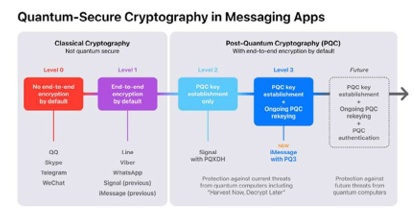
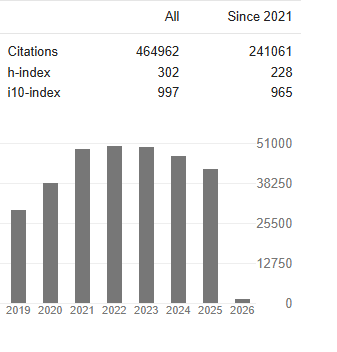
Figure 1: Difference between Classical Encryption and Postquantum Cryptographic Systems
Integrating PQC into existing systems is not a simple task; it requires overhauling current encryption standards, updating software, and ensuring backward compatibility. However, these efforts are crucial for future-proofing digital security [17]. With the potential for quantum computing to disrupt traditional encryption methods, organizations must begin adopting these quantum- resistant algorithms to maintain the confidentiality and integrity of their data in a quantum-powered world.
• Quantum Key Distribution (QKD)
As the threat of quantum-powered cyberattacks looms, Quantum Key Distribution (QKD) emerges as one of the most promising tools to ensure secure communication. Traditional encryption systems rely on symmetric key cryptography, where both parties use the same key to encrypt and decrypt messages. The security of this system relies on the assumption that the key remains secret. However, with quantum computing’s ability to break encryption through algorithms like Shor’s algorithm, this assumption is no longer reliable [18].
Figure 2: Quantum Key Distribution
QKD revolutionizes this concept by using the quantum properties of particles to exchange cryptographic keys securely. The fundamental principle behind QKD is the quantum no-cloning theorem, which asserts that an unknown quantum state cannot be perfectly copied [19]. This means that if an eavesdropper attempts to intercept a quantum key, the quantum state of the particles will be altered in the process, alerting the communicating parties to the breach. This concept of quantum entanglement and the Heisenberg uncertainty principle make it virtually impossible for attackers to obtain information about the key without being detected.
The most widely known QKD protocol is the BB84 protocol, which uses photons to encode and transmit keys. If an eavesdropper tries to intercept the photons, they would inevitably introduce errors in the transmission, alerting the parties involved to the presence of an intruder. By implementing QKD, organizations can ensure that their communication channels remain secure, even in the face of quantum-powered attackers [20]. However, while QKD provides an innovative solution, it is not without challenges. The practical implementation of QKD requires specialized hardware and infrastructure, which are still in the early stages of development. Nevertheless, its potential for safeguarding future communications in a post-quantum world makes it an essential area of research for secure data transmission.
• Strengthening Human-Centric Security
While technological advancements such as PQC and QKD provide robust defenses against quantum threats, human error remains a major vulnerability in cybersecurity. Social engineering attacks, which manipulate individuals into revealing confidential information, are often the weakest link in any organization’s security posture. As cybercriminals increasingly leverage quantum- enhanced tools like deepfakes and advanced phishing techniques, the need for a human-centric security approach becomes even more pressing[21].
One of the most effective ways to mitigate these risks is through behavioral cybersecurity. This approach focuses on educating individuals to recognize the signs of social engineering attacks and respond appropriately. By fostering a culture of awareness, employees and individuals can become the first line of defense against quantum-enhanced phishing schemes, fraudulent impersonations, and other deceptive tactics.
Multi-factor authentication (MFA) is a key component of strengthening human-centric security [22]. By requiring multiple forms of verification, such as passwords, biometric data, and one- time passcodes, MFA creates an additional layer of defense that is much harder for attackers to bypass, even if they manage to obtain one piece of sensitive information.
Beyond MFA, continuous behavioral monitoring is another critical aspect of human-centric security. By tracking user behaviors, organizations can detect deviations from normal activity that may indicate unauthorized access attempts. For instance, if an employee suddenly accesses sensitive files from an unusual location or device, security systems can flag this as a potential insider threat or phishing attempt. Combining educational programs, multi-layered authentication, and continuous monitoring ensures that even in the face of evolving quantum threats, organizations can maintain strong human-centric defenses against social engineering.
• Blockchain for Identity Protection
The increasing risk of identity theft in the quantum era calls for innovative solutions to safeguard personal data. Blockchain technology, with its decentralized and tamperproof architecture, offers a compelling approach to protecting identities. Traditional identity management systems rely on centralized databases where personal information is stored. This centralized model makes these systems vulnerable to cyberattacks, as a single breach could expose the data of millions of individuals [23]. Blockchain addresses these risks by distributing identity data across a decentralized ledger, where it is encrypted and cryptographically secure. The inherent transparency and immutability of blockchain ensure that once data is recorded, it cannot be altered or erased without the consensus of the network. This makes it much harder for attackers to manipulate or forge identity credentials [24].
|
Blockchain Component |
Classical Security |
Quantum Vulnerability |
Potential Post- Quantum Solution |
|
Digital Signatures (ECDSA) |
Strongly secure using elliptic curves |
Breakable using Shor’s algorithm (log(N) complexity) |
Lattice-based Digital Signatures (e.g., XMSS) |
|
Hashing (SHA-256) |
Secure for current classical systems |
Quantum can reduce security via Grover's algorithm |
Quantum- resistant hash functions (e.g., SPHINCS+) |
|
Public-Key Cryptography |
Secure (RSA, ECC) |
Breakable by quantum algorithms (RSA, ECC) |
NTRU, Kyber (Post-Quantum) |
Table 2: Vulnerabilities of Blockchain Systems in the Quantum Era
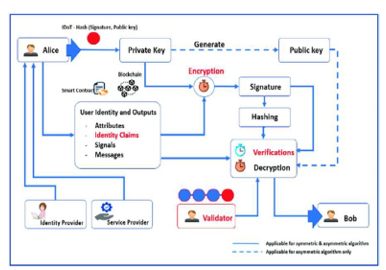
Figure 3: Diagram Illustrating how Blockchain Works for Identity Management
In the quantum era, blockchain can be further enhanced by integrating quantum-resistant encryption techniques, ensuring that the data stored on the blockchain remains secure even in the presence of quantum-powered decryption capabilities. The combination of blockchain’s decentralized nature and post- quantum cryptography would create an unbreachable foundation for digital identity management. Users could have control over their own identity, ensuring that only authorized individuals have access to their personal data, while remaining protected against the risks posed by quantum computing.
This approach could revolutionize online identity verification, making it virtually impossible for attackers to impersonate individuals or steal their credentials. By integrating blockchain with quantum-resistant cryptographic algorithms, organizations can create secure, verifiable identities that stand resilient in the face of quantum-powered cyber threats.
• Adapting Security Protocols for Quantum Resilience
As quantum computing continues to evolve, it is becoming increasingly clear that traditional security protocols will not be sufficient to protect against the new wave of threats. To safeguard against quantum-powered attacks, cybersecurity frameworks must be adapted and strengthened. The shift from current encryption standards to post-quantum algorithms is a necessary first step in this process. These new algorithms, designed to resist quantum decryption methods, will form the backbone of future security protocols.
In addition to transitioning to PQC, organizations should also integrate quantum key distribution (QKD) into their communication systems [25]. By using QKD, sensitive information can be transmitted securely, even in a quantum empowered world. Furthermore, authentication methods must evolve to incorporate quantum-resistant mechanisms, ensuring that even if an attacker gains access to encrypted data, they cannot easily bypass security checks.
Adapting existing security protocols for quantum resilience will require collaboration across industries and disciplines.
Governments, private sector organizations, and cybersecurity experts must work together to develop and implement quantum- adaptive security systems that can evolve in response to emerging quantum threats. Through continuous research and development, the cybersecurity community can ensure that digital systems remain secure, even as quantum technologies reshape the landscape of cyber threats [26].
Case Studies: Exploring Quantum Enhanced Social Engi- neering Threats
As quantum computing continues to evolve, its potential to revolutionize multiple industries grows. However, this power also introduces new, unprecedented risks to cybersecurity. Traditional social engineering attacks, which have long relied on exploiting human behavior and trust, are set to undergo a drastic transformation with the advent of quantum technology. The following case studies illustrate how quantum-enhanced social engineering could be leveraged to bypass conventional defenses and wreak havoc in both everyday communications and highly secure systems like blockchain.
Scenario 1: The Quantum-Enhanced Phishing Attack
Phishing attacks have always been a prominent tool for cybercriminals, using deception to trick individuals into revealing confidential information, such as passwords or credit card details. What makes phishing particularly effective is its ability to prey on human vulnerabilities—trust and urgency.[10] But imagine a future where quantum computing amplifies this deception to a level of sophistication previously thought impossible.
A Hypothetical Scenario:
Picture a cybercriminal who, armed with the computing power of a quantum machine, intercepts encrypted communications. Traditional encryption algorithms like RSA or ECC, which are commonly used to secure email communications, could be cracked with unprecedented speed by quantum computers using advanced algorithms such as Shor’s Algorithm.
The attacker, using quantum capabilities, decrypts private emails exchanged between colleagues in a corporate setting. This gives the intruder full access to personal messages and sensitive information that would normally be protected. From there, the attacker could impersonate a trusted figure— perhaps a senior executive—and send highly convincing emails that prompt a colleague to wire large sums of money or share confidential documents. Since the emails are decrypted and appear entirely legitimate, even the most cautious employees might be fooled [7].
This scenario illustrates the devastating potential of quantum- powered phishing attacks. With quantum decryption capabilities, attackers would not only be able to crack encrypted communications faster but also tailor their phishing attempts with an eerie level of precision, making detection increasingly difficult. The ability to craft such targeted and seemingly authentic messages could allow quantum-enhanced phishing to bypass even the most advanced email filtering and anti-phishing technologies, potentially leading to widespread data breaches or financial theft.
|
Feature |
Traditional Phishing |
Quantum- Enhanced Phishing |
|
Encryption Break Speed |
Time-consuming (hours/days) |
Almost instantaneous (seconds/minutes) |
|
Attack Complexity |
Low (simple impersonations) |
High (targeted, precise attacks) |
|
Detection Difficulty |
Medium (filters can detect patterns) |
Very high (quantum- powered decryption makes detection harder) |
|
Success Rate |
Varied (depends on victim awareness) |
Potentially much higher (no barriers to breaking encryption) |
Table 3: Comparison of Traditional vs Quantum-Enhanced Phishing Attacks
Scenario 2: Quantum Social Engineering in Blockchain Systems
Blockchain technology is lauded for its decentralized nature, offering robust security features and transparency. The backbone of this security relies heavily on encryption— specifically, public- private key pairs and hash functions— that protect users' identities and assets. However, the rise of quantum computing poses a fundamental threat to these very encryption methods, potentially exposing vulnerabilities within blockchain networks.
A Hypothetical Scenario
In this case study, we explore how quantum computing could disrupt blockchain security. Although blockchain is known for its robustness, its reliance on cryptographic techniques makes it susceptible to the power of quantum algorithms. With the ability to crack the encryption that underpins blockchain systems, a quantum attacker could gain unauthorized access to blockchain wallets and private keys.
The attack would begin with the quantum-powered decryption of the public-private key pair, enabling the cybercriminal to impersonate a legitimate user or manipulate transactions. Imagine a blockchain user receiving a fraudulent transaction request that looks perfectly legitimate, seemingly coming from a trusted source like a cryptocurrency exchange. The attacker, using quantum decryption, could alter transaction details, reroute funds, or even create entirely new transactions that appear legitimate [24].
Moreover, such an attacker could forge blockchain-based identities, making it difficult to distinguish between a real user and a quantum-impersonated one. This could open the door to fraudulent transactions, unauthorized access, and even the theft of assets from users' blockchain wallets.
|
Quantum - Enhanced Attack |
Affected Blockchain Component |
Attack Mechanism |
Potential Consequence s |
|
Quantum Decryptio n of Keys |
Public Key Infrastructure (PKI) |
Breaking of private keys, allowing attackers to forge signatures |
Identity theft, unauthorized transactions |
|
Quantum- Spoofing of Signatures |
Digital Signatures (ECDSA) |
Quantum computer breaks elliptic curve signatures |
Fraudulent transactions, impersonation of key users |
|
Quantum Brute- Force of Hashes |
Blockchain Hashing (SHA-256) |
Grover's algorithm reducing the complexity of finding valid blocks |
Compromise of blockchain integrity, double- spending |
Table 4: Blockchain Vulnerabilities Exploited by Quantum Enhanced Social Engineering
This scenario showcases how quantum-enhanced social engineering could target the trust mechanisms at the heart of blockchain technology. The system’s reliance on traditional cryptographic safeguards, which are vulnerable to quantum decryption, could lead to massive breaches in digital identity security and financial transactions. Even decentralized systems, once thought impervious to traditional hacking methods, would be at risk, highlighting the urgent need to future-proof blockchain against quantum threats.
Figure 4: An Infographic Showing Phishing, Smishing, and Dumpster Diving as Part of Quantum-Enhanced Social Engineering
These case studies underscore the transformative threat posed by quantum computing to modern cybersecurity infrastructure. As quantum technologies advance, they will not only challenge the core principles of current encryption systems but also dramatically enhance the effectiveness of social engineering attacks. To combat these evolving risks, cybersecurity must evolve to keep pace, integrating new technologies and strategies capable of defending against the quantum-enabled threats of tomorrow.
Conclusion
The introduction of quantum computing signals a transformative shift in the landscape of cybersecurity, particularly through the rise of Quantum Social Engineering. This research has highlighted the potential threats quantum technologies pose by amplifying traditional social engineering attacks such as phishing, identity theft, and impersonation. As quantum capabilities evolve, attackers will gain unprecedented power to bypass conventional encryption, manipulate human vulnerabilities, and exploit security flaws that were previously considered safe.
The study emphasizes the critical importance of transitioning to quantum-resistant cryptographic systems and adopting Quantum Key Distribution (QKD) to ensure secure communication in the quantum era. While the technological advancements of quantum computing pose significant challenges, they also present opportunities to rethink and strengthen cybersecurity frameworks. By focusing on human-centered security protocols and behavioral cybersecurity practices, organizations can better protect themselves against sophisticated social engineering tactics that will emerge in a quantum-powered world.
Ultimately, this paper underscores the urgency for both technological innovation and adaptive defense strategies in response to quantum threats. The future of cybersecurity lies in the development of resilient systems that can withstand quantum computing’s disruptive potential. Preparing for the post-quantum era is not just a necessity but an imperative to safeguard digital infrastructures and protect against Quantum Social Engineering attacks.
Future Directions
As quantum technologies continue to develop, cybersecurity strategies must evolve accordingly. Some key areas for future research and development include: Development of Post-Quantum Cryptographic Standards: While promising post-quantum cryptographic (PQC) algorithms exist, standardization efforts need to be accelerated to ensure widespread adoption. Organizations like NIST are working toward defining PQC protocols, but more real-world testing is necessary [22].
Advancements in Quantum Key Distribution (QKD)
Infrastructure
QKD offers a theoretically unbreakable encryption method, but its large-scale deployment faces technical and logistical hurdles. Future research should focus on improving QKD scalability, reducing costs, and integrating it with existing cybersecurity infrastructures [19].
AI-Driven Threat Detection in Quantum-Aware Cybersecurity
The integration of machine learning (ML) and artificial intelligence (AI) with cybersecurity can enhance threat detection and adaptive defense mechanisms against quantum-powered social engineering attacks [12]. AI-based fraud detection, particularly in deep fake detection and anomaly-based phishing detection, will be crucial [22].
Human-Centric Cybersecurity Awareness and Training
With quantum-enhanced social engineering becoming more advanced, cybersecurity education must be updated to include awareness of AI-generated deep fakes, quantum enabled phishing, and identity forgery techniques. Organizations should incorporate behavioral cybersecurity training for employees and users [11].
Quantum-Secure Blockchain and Digital Identity Protection
Blockchain technology is at risk due to its reliance on traditional cryptographic techniques. Future research should explore the development of quantum-secure blockchain protocols that incorporate quantum-resistant digital signatures and secure distributed ledger technologies [24].
Collaboration Between Governments, Academia, and Industry
Quantum cybersecurity is a global challenge. Governments, academia, and private industry must work together to develop policies, frameworks, and international standards for securing digital infrastructure in the quantum age. Public-private partnerships will be vital in addressing emerging quantum cyber threats [26].
Final Thoughts
Ultimately, this paper underscores the urgency for both technological innovation and adaptive defense strategies in response to quantum threats. The future of cybersecurity lies in the development of resilient, quantum-secure systems that can withstand the disruptive potential of quantum computing. Proactive research, collaboration, and strategic implementation of quantum-resistant technologies will be key to ensuring a secure digital future. Preparing for the post-quantum era is not just a necessity but an imperative to safeguard digital infrastructures and protect against Quantum Social Engineering attacks.
References
- Cao, Y., & Zhou, Y. (2020). Quantum cryptography: A practical introduction. IEEE Transactions on Circuits and Systems I: Regular Papers, 67(9), 3349–3362.
- Nielsen, M. A., & Chuang, I. L. (2010). Quantum computation and quantum information. Cambridge university press.
- Ding, X., & Lee, K. C. (2020). Quantum-safe cybersecurity: The need for post-quantum cryptography. Journal of Information Security and Applications, 53, 102531.
- Shevchenko, M. (2021). Quantum social engineering: New paradigms of cybersecurity. Quantum Computing and Cybersecurity Journal, 3(1), 15–30.
- Mosca, M. (2018). Cybersecurity in a quantum world. Nature Electronics, 1(4), 160–162.
- Jorfi, S., & Gorski, P. (2020). Exploring quantumenhanced phishing: How quantum computing could revolutionize phishing techniques. Journal of Quantum Technologies, 5(2), 44–56.
- Taylor, B., & Langford, R. (2021). Quantum computing: A new era for cryptography and digital security. IEEE Transactions on Information Forensics and Security, 16, 1031–1040.
- Schumacher, D., & Bianchi, J. (2019). Protecting critical infrastructure with quantum-aware cybersecurity systems. Quantum Networks and Communication Systems, 13(5), 233– 245.
- Finkelstein, A. (2019). Quantum computing and its implications for digital identity security. International Journal of Security and Privacy, 13(4), 92–110.
- Yang, J., & Wang, X. (2018). Cybersecurity threats in the quantum computing age. Computers & Security, 77, 308–321.
- Qian, Z., & Yu, X. (2020). Exploring the impact of quantum computing on digital identity management systems. Proceedings of the ACM Conference on Quantum Computing and Cybersecurity, 97–105.
- Gritti, G., & Rane, S. (2021). Quantum cryptography: Applications in blockchain and next-generation security systems. Journal of Cryptographic Engineering, 11(2), 151– 165.
- Krenn, M., et al. (2020). The future of quantum-safe cryptography: Advancing post-quantum algorithms. Journal of Cybersecurity, 10(1), 1012-1031.
- Lofaro, D., & Hasheminejad, A. (2019). PostQuantum Cryptography: A Survey of Algorithms and Protocols. Springer Briefs in Computer Science
- Matsumoto, T. (2020). Lattice-based cryptography and its applications to post-quantum encryption. IEEE Access, 8,184392–184403.
- Smeets, G., et al. (2020). Post-quantum cryptographic algorithms: A comparative analysis. IEEE Access, 8, 109234- 109247.
- Chen, L., et al. (2016). Post-Quantum Cryptography: Current State and Future Directions. NIST Special Publication-800-145.
- Bennett, C. H., & Brassard, G. (1984). Quantum cryptography: Public key distribution and coin tossing. Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, 175–179.
- Hwang, T., et al. (2003). Quantum key distribution with entangled photons. Physical Review A, 67(2), 022305.
- Van Assche, G., & Tittel, W. (2020). Quantum security protocols for post-quantum internet: Ensuring safety in the quantum era. Quantum Information Science & Technology, 6(1), 123–145.
- Bernstein, D. J., et al. (2018). Post-quantum cryptography:Current state and challenges. Communications of the ACM, 61(3), 42–45.
- Sundaram, P., & McShane, B. (2021). Advancements in quantum cryptography: A review of post-quantum cryptographic methods. Computers & Security, 108, 102325.
- laus, D., & Sklar, B. (2020). Quantum-safe cryptography for securing critical infrastructures: Prospects and limitations. Future Generation Computer Systems, 104, 34-47.
- Shankar, S., & Vohra, P. (2021). Quantum-aware cybersecurity for blockchain systems: Ensuring the integrity of decentralized applications. Journal of Blockchain Technology and Applications, 3(2), 50-67.
- Jalali, M. (2021). The state of quantum-aware cryptography: Can post-quantum algorithms protect us? Quantum Information & Processing, 20(8), 1–25.
- Chakrabarti, A., & Agrawal, R. (2021). Leveraging quantum computing for cybersecurity risk management: A post- quantum cryptographic approach. Cyber Risk and Security Analytics, 6(3), 32-46.