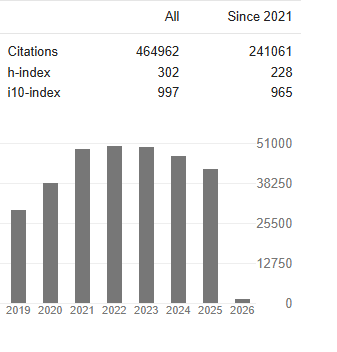
Research Article - (2024) Volume 2, Issue 1
Physical and Data Link Layer Performance Enhancement in MANET to Overcome Hidden -Exposed Node Problem and Packet Loss Due to Buffer Overflow
2Vice Chancellor and Professor , Manipur International University , Imphal , Manipur, India
3CTO& Dean Innovation , Manipur International University , Imphal ,Manipur, India
Received Date: Dec 05, 2023 / Accepted Date: Dec 26, 2023 / Published Date: Jan 08, 2024
Copyright: ©Ã?©2024 S. Hemalatha, et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Citation: Hemalatha, S.. Pallathadka, H., Chinchewadi, R. P. (2024). Physical and Data Link Layer Performance Enhancement in MANET to Overcome Hidden -Exposed Node Problem and Packet Loss Due to Buffer Overflow. Int J Med Net, 2(1),01-08.
Abstract
In order to improve the performance of the MANET , the lower layers of MANET protocol stack has to improve the performance to overcome the hidden and expose node problem in the Physical layer and better buffer management scheme to be included in the data link layer .MAC layer in MANET ,Some cases the transmission range of the node can be idle but due to Hidden and Exposed node , the node could not be send the packet to other nodes. Node has to wait unnecessarily event the transmission medium is free. In case of more traffic in the MANET can leads to overflow in the buffer which causes the packet loss in the transmission. If any packet missed on the transmission the source node has to retransmit to the destination. This research article proposed the Mutual Exclusion MAC protocol for avoiding hidden and exposed terminal problem in MANET and active buffer management algorithm named Intelligent better buffer management (IBM) algorithm which improves the MANET nodes buffers to avoid packet loss . The proposed protocol is implemented with the support of Network simulator 3 and results are compared with the existing different protocol proposed for the MAC layer with the parameter and buffer management schemes and results shown the enhanced results shown.
Keywords
Manet, Hidden and Exposed Nodes, Buffer Management , MAC protocol.
Introduction
Mobile Adhoc Network (MANET) is a kind of wireless data communication devices which rely on communication among the node without infrastructure and any access point. The protocol stack of MANET follows the OSI protocol stack ,every layer is assigned responsibility of processing data for transmission. For instance, the physical layer is responsible for transmitting the packet over the medium , Data link layer is for diving packet in to frame, Network layer is for finding the best route for packet transmission transport layer is for reliable packet transmission over TCP or UDP protocol.
MANET MAC protocol are in two classification lie contention based scheme and Contention free scheme. The TDMA,CDMA and FDMA are comes under contention based scheme used to avoid contention. contention free scheme are static network with centralized node control [1].
Again contention based MAC protocol is further classified in to two more category like Random access protocol and dynamic Reservation Collision Resolution protocol. Pure aloha and slotted Aloha are under Random access protocol, CSMA belongs to Dynamic Reservation Collision Protocol. Contention based MAC protocol further classified in to single channel, multi channel ,directional antenna based, power aware and QoS aware schemes [2]. The Classification of MAC protocol depict in the figure 1.1 shown below.
Figure 1.1: Classification of MAC Protocols
From the Table 2.1,which summaries about the related research work proposed towards MAC protocol implementation of overcome the Hidden and Exposed terminal problem [3,4]. Many of the authors centric on RTS/CTS mechanism which solves the collision in hidden terminal but fails on exposed terminal problem. Another Set of authors concentrates on usages of directional and Omni directional antenna to overcome the Hidden and Exposed Terminal problem but this also fails on giving solution to exposed problem [5].
Finally single channel and multi channel adoption with data streaming also support the MAC protocol implementation that mechanism also fails on the overcome the problem. Still the need of new protocol invention to resolve the MAC layer Hidden and Exposed Terminal problem. This article focus on the new MAC layer Protocol named Mutual Exclusion MAC Protocol with the support of Hidden and Exposed table creation among the MANET nodes.
|
S.No |
Authors |
Invented Mechanism Used |
|
1 |
Caishi Huang et all |
RTS/CTS mechanism DATA broadcast. |
|
2 |
Viral V. Kapadia |
RTS/CTS mechanism with omni directional antenna. |
|
3 |
Ms. Ritu Patidar et. al |
MAC protocol with antenna support. |
|
4 |
Lu Wang et. al |
Attachment Coding technique was suggested attaching control information to data stream. |
|
5 |
Khaled H. Almotairi et. al |
MMAC -HR resolving the exposed terminal problem. |
|
6 |
Ketema Adere, Ramamurthy |
Omni directional and directional antennas based MAC Protocol. |
|
7 |
KiHong Kim et. |
MAC light weight low power authentication mechanism |
|
8 |
. Caishi Huang , Chin-Tau Lea , Albert Kai-Sun Wong |
|
|
9 |
Viral V. Kapadia, Sudarshan et .. all |
Adhoc network with control schemes like RTS/CTS mechanism. |
|
10 |
Chen J, Sheu S, Yang C |
R-CA named for dynamic channel interference which made for channel assignment. |
|
11 |
Liu K, Wong T, Li J, et al |
Simple DCF MAC protocol allows the parallel transmission. |
|
12 |
Liu Kai*, Xing Xiaoqin |
Back - off criteria used by the Virtual Base Station |
|
13 |
Lu Wang, Kaishun Wu,Mounir Hamdi |
Virtual jamming that could prevent the various problems of RTS /CTS problem. |
Table 2.1: Literature Review Summary
The new queue management scheme proposed by Kulkarni et al against the traditional RED queue management named PAQMAN [6]. In this method the queue size is varies based on the traffic in MANET .This technique improves the Quality of service comparing with RED . Hop based queuing method proposed by Friderikos and Aghvami , The packet drop is based on the number of hops the packet traversal which recedes the excess delay in TCP flow control mechanism [7]. Lutz et al proposed the focusing on the packet flow is the same order of packet created this causes the increased the throughput and reduce the packet loss [8]. Drop tail queue management system proposed by Chen and Bensaou with multiple congestion link forms in high speed network in MANET which shown that proposed methods faces the unfairness in dropping packets as well as round trip time unfairness and round trip time unfairness [9].
Effective RED algorithm proposed by Abbasov and Korukoglu variation incorporated in RED packet dropping function which produced the better throughput and packet loss [10].Size oriented Queue management proposed by Dimitriou and Tsaoussidis forms the size based on the traffic , scheduling packet flow this parameter supports improvement in queue management strategies [11]. Dynamic buffer space introduced by Muhammad Aamir et al which support for avoiding the packet drop in MANET. choke packet mechanism proposed by Mr. A. Chandra finds out the additional overhead traffic and maintains the virtual queue [9,12]. Queue management technique analysis is done by P.T.Mahinda with the support of allocating the packets in TCP flow and compared the result with RED and REM shows the better improvement [13]. In the dell bell technology different queue maintenance technique comparison is done by Shubhangi Rastogi , the result shown that Non Linear Random Early Detection technique is the better queue management technique [14] .
This paper is organised as follows: introduction in section 1, necessity for protocol stack in section 2, suggested MAC and buffer management technique in section 3, implementation results in section 4, and conclusion in section 5.
Protocols Stack Necessity
The Proposed Mutual Exclusion MAC protocol incorporates by maintaining the table called Hidden and Exposed nodes table which support for doing MEMAC protocol works. In order to create the Table, The MANET every nodes region assumes as a Ven Diagram plotting [15]. The union intersection, Symmetric difference, relative symmetric, absolute complement of the Ven diagram notations are support for the Table creation . The Details of the Ven diagram logical relationship and the set shown in the Figure 2.1 below .
Figure 2. 1: Logical Relationships of Ven Diagram
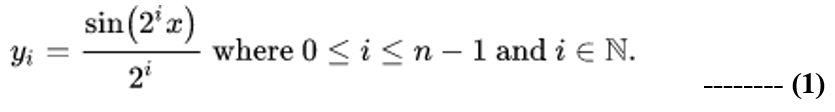
A ven diagram is also called set diagram or logic diagram which support to show all possible logical relationship between the set. In this research paper uses ven diagram for each set S defines as a node A under the region all the other nodes . likewise for all other nodes sets are defines as well periodic updated . The research focus on extension of higher number of sets probably takes four intersection forms a spheres, to 16 intersection of 16 cell. The n set diagram for different topologically diagram sin curve equation is shown below equ 1 .
From the Literature survey all the three category of the buffer management techniques will be done in passive , active and proactive buffer management still the research is needed for proposing the new method to overcome the packet drop in MANET .Passive buffer management technique applies when the buffer is full , active buffer management applied before buffer is full and proactive is relay on the TCP congestion control .All the categories does not provide the reliable solution for managing the buffer effectively .
Novel algorithm is proposed in this article which monitoring the buffer capacity and applies the strategy on the buffer when the buffer is in half of the capacity. This proposed algorithm always keeps the buffer capacity in between fifty percent to ninety percent. The reason for maintain the range in the buffer size to control the congestion control in the MANET .
MAC and Buffer Management Protocol
MAC Protocol
In order to overcome the Hidden and Exposed terminal problem in the MANET Physical layer challenges there are the several techniques are proposed , but all the proposed method are having the pits and fall on it . In this article proposed the Mutual exclusion Protocol for MAC layer by maintain the hidden and exposed terminal in each node which support to Finding out hidden and exposed terminal in each region.
Mutual Exclusion MAC (ME-MAC ) Protocol Works as
Follows in the Stages.
1. For all the nodes in the MANET form the region Maintain the hidden and Exposed node table
2, Generate the beacon signal by collecting the node available position
3. Upon receiving the node position form the nodes which are in the nodes region called the SET node a single node region
Hidden Node Table Creation
1. MANET Set of NODEs N = Node { n1 ,n2,n3,. nm } m is a total number of nodes in a MANET
2. For each node i from 1 to N Generate location aware of other node in each i th node transmission range
3. All the node share the nodes which are in the region to its Transmission range nodes .
4. Repeat for ( i=1 to N)
{
Select adjacent three nodes one by one n i, n i+1,n i+2 Hidden node of ni = n i+2 if ni -> n i+1, n i+1 -> n i+2 then n i -> n i+2 .
Also in generalize
Hidden node of n i = (List of nodes in ( n i)U (n i+1) U (n i+2)) ~ ((List of node n ith node transmission range ) U (List of node in n i+1th transmission range ))
}
Exposed Node Table Creation
1. MANET Set of NODEs N = Node { n1 ,n2,n3,. nm } m is a total number of nodes in a MANET.
2. For each node i from 1 to N Generate location aware of other node in each i th node transmission range
3. All the node share the nodes which are in the region to its Transmission range nodes .
4. Repeat for ( i=1 to N)
{
Select adjacent Four nodes one by one n i, n i+1,n i+2, n i+3 Exposed node of n i+1 = n i+3 if ni -> n i+1, n i+2 -> n i+3 then n i +2 and n i+2 are exposed nodes . Also in generalize Exposed node of i = If i and j are in the same transmission range and List of node ith node transmission range is not equal to List of node in jth transmission range then i is exposed node to j
}
Buffer Management
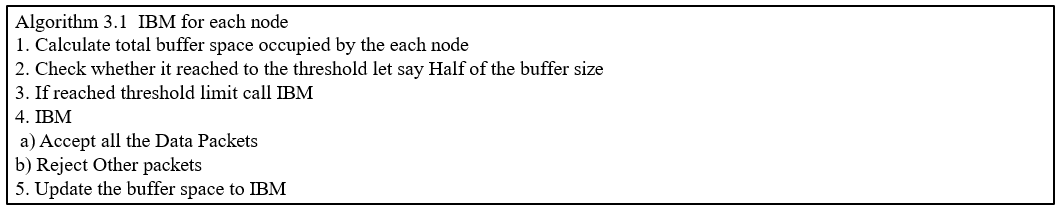
The proposed MANET active buffer management algorithm names as Intelligent Buffer Management (IBM) . Receiving buffer information could be in the category of actual packets , router request, router reply, synchronization, Ack etc. This algorithm keeps tracking the buffer size information when the buffer size becoming half of the buffer size automatically this algorithm will invoke the controlling the packet. This algorithm start checking of the buffering information , except reliable data packet and remaining all the category of the packet are dropped from the buffer . The details work flow is explained in the pictorial representation from the Figure 3.1 and details of the IBM algorithm steps shown in the table 3.1 . This is achieved by for every second the Sample Interval queue size (SIQS) is estimated and also the estimated Queue threshold level(EQTL) is estimated by using the calculation of total queue size/ 2 . For each packet arrival to the buffer queue , current queue length (cql) is compared with estimated Queue threshold level (eqtll ),if (cql) < (eqtll ) then allow all the incoming packet in to the queue for forwarding otherwise the IBM algorithm is invoked to drop the non data packets in the Queue. The targeted queue delay Qd in each node is estimated by using the equation
Qd = targetDelay * ptc,
where ptc = linkBandwidth(bits)/(8 ![]() meanPktSize).
meanPktSize).
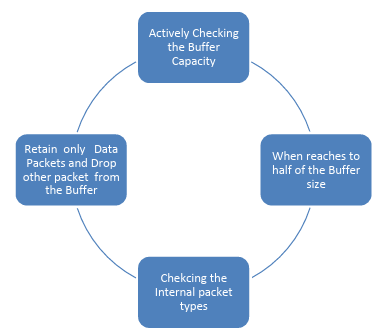
Figure 3.1: Work Flow of IBM Algorithm
Algorithm 3.1 Intelligent Buffer Management Algorithm for each Buffer
Results and Discussion
The Proposed Mutual Exclusion MAC protocol is implemented with the Network simulator 3with total 250 nodes designed in and following the Parameter set up in table 5.1. Two new signal are added with the Network simulator for giving solution to the Hidden and Exposed Terminal Mutual Exclusion agreement name as Hidden signal and Exposed Signal. Every beacon signal updated the table of Hidden and exposed nodes in the MANET, when a nodes want to communicate with the other nodes it check the medium is free also check the Hidden and exposed nodes updated table. If the source node is Hidden node, the node could not wait to the medium become free , as well as the Exposed nodes follows the same . Initially the NS3 GUI is plotted and show the Collision possibilities with the support of Hidden and Exposed Terminal nodes . Initially three nodes are plotted to show the collisionN1, n2 and N3 are the MANET nodes , N1 and N2 wants to communicate with the N3 , both sense the carrier it is free then both N1 and N2 start sending the packet , but collision occur at the N3. To come such a scenario the two signals are generated Hidden and exposed signal to make mutual agreement on sending the packet to the destination.
|
S.No |
Parameter |
Value set |
|
1 |
PHY |
DSSS |
|
2 |
CWmin |
32 bit |
|
3 |
CWmax |
1024 bit |
|
4 |
Channel Data Rate |
11Mbps |
|
5 |
Basic Data Rate |
1Mbps |
|
6 |
SIFS |
15 µs |
|
7 |
DIFS |
45 µs |
|
8 |
Slot time |
15 µs |
|
9 |
Propagation delay |
1 µs |
|
10 |
Packet Payload |
10000bits |
|
11 |
MAc Header |
200 bits |
|
12 |
PHY Header |
150bits |
|
13 |
ACK |
250 bits |
|
14 |
RTS |
250 bits |
|
15 |
CTS |
250 bits |
|
16 |
Hidden signal |
250 bits |
|
17 |
Exposed Signal |
250 bits |
Table 5.1: Network Simulator Parameter Setup
In order to compare the performance the proposed ME-MAC protocol is compared with the existing protocol in shown in the Table 2.1 methods. The Methods taken for comparisons are RTS/CTS , MAC protocol , simple DCF MAC an parameter are packet drop due to transmission rate , broadcast received . Simulation nodes are placed in 500m*500m with constant increasing the nodes from 1 to 100. Maximum speed of each node varies from 0 to 10 m/.s
Case 1. When simulation made static and traffic increases the ME-MAC performs high delivery ratio over 85 % compare to the existing protocols shown in the Figure 5.2 result graph. Throughput is better than existing but there no variation on the power consumption.
Figure 5.2: ME-MAC Packet Delivery Ratio Analysis with Other Methods
Case 2. When a nodes moves in the speed of maximum 10m/s the drastic packet delivery ratio in the existing protocol, even some performance slow down in ME-MAC due to the updating of hidden and exposed terminal maintenance table and Hidden and exposed signals.
Figure 5.3: ME-MAC Packet Delivery Ratio Analysis With other Methods
Case 3. When the packet drop due to node mobility or collision causes retransmission of packets. The ME- MAC protocol support avoiding the collision and retransmission of packet reduced to 25 % comparing with the existing protocol scenario as depicted in the Figure 5.4 . The ME-MAC Protocol works well even the number of nodes increases in the MANET
Figure 5.4: ME-MAC Packet Drop Analysis with Other Methods
Case 4. The Impact of Hidden and exposed Signals introduces in the MANET , MAC layer which support the broadcast of hidden and exposed nodes which makes a greater number of routing path selection among the MANET
Figure 5.5: ME-MAC Route Selection Analysis with other Methods
Conclusion
The Proposed ME-MAC protocol for MAC layer helps to support to create the hidden and exposed nodes in MANET nodes, which reduced the nodes waiting for the medium become free even the medium is free. Also this protocol support the MANET performance in comparing with the existing MANET MAC Methodology .In feature this Protocol can be incorporate to the data link layer for forming the enhanced MANET protocol with overcoming many challenges in the MANET protocol issues.
References
- Xu, S., & Saadawi, T. (2001). Does the IEEE 802.11 MAC IEEE communications Magazine, 39(6), 130-137.
- Huang, C., Lea, C. T., & Wong, A. K. S. (2012). A joint solution for the hidden and exposed terminal problems in CSMA/CA wireless networks. Computer networks, 56(14), 3261-3273.
- Kapadia, V. V., Patel, S. N., & Jhaveri, R. H. (2010). Comparative study of hidden node problem and solution using different techniques and protocols. arXiv preprint arXiv:1003.4070.
- Ketema Adere, Rammurthy, “Solving the Hidden and Exposed Terminal problems Using
- Directional-Antenna Based MAC Protocol for Wireless Sensor Networks” 7th International
- Conference on Wireless and Optical Communication Networks, Colombo(2010).
- Ramanathan, R., & Redi, J. (2002). A brief overview of ad hoc networks: challenges and directions. IEEE communications Magazine, 40(5), 20-22.
- Kulkarni, P. G., McClean, S. I., Parr, G. P., & Black, M. M. (2006, April). Proactive predictive queue management for improved QoS in IP networks. In International Conference on Networking, International Conference on Systems and International Conference on Mobile Communications and Learning Technologies (ICNICONSMCL'06) (pp. 7-7). IEEE..
- Friderikos, V., & Aghvami, A. H. (2003, December). Hop based queueing (HBQ): an active queue management technique for multihop wireless networks. In Fourth International Conference on Information, Communications and Signal Processing, 2003 and the Fourth Pacific Rim Conference on Multimedia. Proceedings of the 2003 Joint (Vol. 2, pp. 1081-1085). IEEE.
- Lutz, J., Colbourn, C. J., & Syrotiuk, V. R. (2012). Variable weight sequences for adaptive scheduled access in MANETs. In Sequences and Their Applications–SETA 2012: 7th International Conference, Waterloo, ON, Canada, June 4-8, 2012. Proceedings 7 (pp. 53-64). Springer Berlin Heidelberg.
- Chen, S., & Bensaou, B. (2007). Can high-speed networks survive with DropTail queues management?. Computer Networks, 51(7), 1763-1776.
- Abbasov, B., & Korukoglu, S. (2009). Effective RED: An algorithm to improve RED's performance by reducing packet loss rate. Journal of Network and Computer Applications, 32(3), 703-709.
- Dimitriou, S., & Tsaoussidis, V. (2010). Promoting effective service differentiation with Size-oriented Queue Management. Computer Networks, 54(18), 3360-3372.
- Aamir, M., & Zaidi, M. A. (2013). A buffer management scheme for packet queues in MANET. Tsinghua Science and Technology, 18(6), 543-553.
- Mahida, P. T., Patel, K., Vanza, N., & Patel, S. (2013). A comparative analysis of queue management techniques using NS-2 simulator. International Journal of Computer Applications, 65(6).
- Rastogi, S., & Srivastava, S. (2014). Comparison Analysis of Different Queuing Mechanisms Droptail, RED and NLRED in Dumb-bell Topology. International Journal of Advanced Research in Computer and Communication Engineering, 3(4), 6286-6288.
- 1https://en.wikipedia.org/wiki/Venn_diagram.