Research Article - (2023) Volume 1, Issue 1
Novel Routing Algorithm for Efficient Packet Transmission in MANET using T-Test Procedure and Sleep and Awake Strategy
2PhD, DSc, Vice Chancellor and Professor, Manipur International University, Imphal , Manipur, India
3CTO& Dean Innovation, Manipur International University, Imphal, Manipur, India
Received Date: Nov 10, 2023 / Accepted Date: Nov 30, 2023 / Published Date: Dec 11, 2023
Copyright: ©Â©2023 S. Hemalatha, et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Citation: Hemalatha, S., Pallathadka, H., Chinhewadi, R. P. (2023). Novel Routing Algorithm for Efficient Packet Transmission in MANET using T
Abstract
Packet transmission is one of the time-consuming communication processes in a mobile ad hoc network. Many routing pathways may encounter failed packet delivery as a result of the MANET node's power backup. The routing algorithm determines the path packets follow as they travel from the source to the destination nodes, but it provides no assurances about packet delivery. This work suggested a new routing method that uses the T-test procedure to discover the most effective path between nodes. This proposed technique recursively identifies the optimum way between nodes for communication, ensuring that each node participating in route discovery has enough energy for transmission.. The T-Test procedure defines and supports the criteria for evaluating the nodes that are chosen and rejected during the route discovery process. This technique, in conjunction with T-Test, enables successful packet transmission in MANET packet flows with sleep and awake strategies. It is also developed using network simulation and compared to the present routing system, indicating that it performs better overall.
Keywords
MANET, Sleep and Awake Strategy, Routing Algorithm, T-Test,
Introduction
An ad hoc network's topology is dynamic, nodes in a mobile ad hoc network (MANET) are unaware of their network's topology and must figure it out on their own. According to the fundamental criteria, whenever a new node joins an ad hoc network, it must broadcast an announcement of its presence and must also pay heed to analogous announcement broadcasts from existing mobile nodes.
Proactive routing systems are sometimes known as table-driven routing protocols. Every mobile node has its own routing database, which lists the routes to all potential destination mobile nodes. Because the topology of a mobile ad hoc network changes often, these routing tables are routinely changed. Its downside is that it struggles with large networks since storing route information to every potential node causes the routing table entries to become excessively large.
Reactive routing systems are sometimes known as on-demand routing protocols. In this type of routing, the path is only discovered when it is required. To accomplish route discovery, route request packets are disseminated over the mobile network. Its two fundamental aspects are route discovery and route maintenance.
A t-test is used in statistics to compare the means of two groups. It is commonly used in hypothesis testing to assess whether two groups vary or whether a method or treatment has an effect on the population of interest. The null hypothesis (H0) asserts that there is no difference between these group means. The actual difference, according to the alternative theory (Ha), is not zero.
A t test (also known as a pairwise comparison) should be used only when comparing the means of two groups. If you want to compare more than two groups or perform several pairwise comparisons, use an ANOVA test or a post-hoc test. The t test is a parametric difference test, which implies that its conclusions are based on the same premises as other parametric tests. The t test assumes that your data are comparable in terms of variation within each group being compared, independent, and (nearly) consistently distributed (also known as variance homogeneity).
MANET Routing Protocol Characteristics
To avoid routing difficulties in MANET, routing protocols should have the following characteristics:
• It should be widely distributed.
• Localization is required.
• It should be adaptive to frequent changes in topology caused by node mobility.
• It must be free of impassable paths.
• The paths must shortly converge.
Performing a T- test The t test evaluates the true difference between two group means by dividing the difference in group means by the total standard errors of both groups. It can be calculated automatically or manually using statistical analysis software and a formula test equation
The formula for the two-sample t test, also known as the Student's t-test, is provided below.
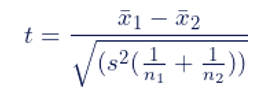
t represents the test statistic, x1 and x2 represent the two groups being compared, s2 represents the combined standard error of the two groups, and n1 and n2 represent the number of observations in each group. A larger t value implies a more significant difference between groups since the difference between group means is greater than the pooled standard error.
Relevant work
Because MANETs are dynamic, there are resource, routing, and stability difficulties, all of which are vulnerable to various attacks. The present literature study highlights the importance of energy conservation as a critical aspect in routing algorithms for network performance and proposes an effective energy algorithm based on the shortcomings of existing energy protocols. The protocols demonstrate the significance of routing in networks and explain the various routing algorithm approaches provided by MANET. Furthermore, it introduces and investigates network security issues, describes intrusion detection methods for network attacks, and proposes improving the energy technique by including a security algorithm.
The network performs badly due to the MANET architecture's fragmented and often dynamic nature. The capacity of this routing protocol to swiftly discover the best paths between sources and destinations ensures that data is transmitted reliably and within the time limit specified. The route path's establishments must adhere to the least amount of overhead. Current routing methods are built for static environments and are incapable of adapting to often changing topologies, resulting in poor convergence, throughput, route loops, overhead, and congestion [1]. This should be enhanced; thus the routing should be properly explored. Security policy methods have been developed for the many types of infrastructure networks.
It is a significant task to implement these policies in MANETs apps. To establish secure paths between source and destination, the authors used a piece of their research on secure routing algorithms [1]. Global Transitions Proceedings 3 (2022), R. Prasad and Shivashankar. The authors of paper proposed a method that minimises overall energy usage while also enhancing network networking lifetime by combining compressive sensing techniques with network coding in the sensor network. By establishing the virtual coordinates, it decreases the energy required to ensure a long-lasting network. This procedure must also accommodate a changing network environment [2].
The research evaluated the energy consumption parameters that affect network longevity. Among the energy consumption factors are the expected energy sources, the energy placement target, and the frequency and latency of data aggregation energy network concentration. A single sink location outperforms several sink sites with limiting network mobility. [3,4].
Although this algorithm consumes the least amount of energy, it fails in high-speed connections because it broadcasts. Messages are constantly passing via the network, and the total overhead is significantpresented a technique for limiting the nodes' energy threshold for message forwarding [5]. The authors presented energy-efficient routing, which builds with multiple route paths in decreasing order, measures the energy levels of each road, introduces new paths, and extends network lifetime [6]. When constructing the paths, the conventional DSR routing protocols do not take energy into account. Both AODV and DSR make efficient use of resources, save energy, and allow mobile ad hoc network architectures/organizations to self-organize, self- configure, and move. Nonetheless, with limited abilities, more flexible, and Nodes in the setup should fulfil the trust tier and routing tier for information transfer [7]. If the node is not prepared to recognise these levels, it will be unable to join the network.
Following the distribution of inquiries over the network, each node can accept one route request from another node. These policy enforcement mechanisms are primarily meant to create safe network paths and routing; nonetheless, they fall short in defending against malicious nodes and various types of attacks. It was described in the study how to build secure channels by broadcasting information hop by hop to authenticate nodes [8]. The network's security protocol then validates end-to-end performance metrics using a symmetric key generated device. Many academics have focused on problems with secure routing paths that use the least amount of energy for transmission and have also raised security concerns about it, but they are ineffectual and struggle when dealing with various types of real- time attacks.
In MANET, there are two sorts of attacks: active and passive. Passive attacks are most common in the TCP/IP network levels and data connection layers. Such attacks have no effect on how the network runs because they ingest packet information from available network nodes. Typically, attacks send data while exchanging information. These assaults have a lower impact on the network than active attacks. These attacks produce disturbances such as information spying, packet loss, and misinformation about nodes. Eavesdropping, jamming, selfish behaviour, traffic analysis, and traffic monitoring are all examples of passive attacks.
Active attacks involve nodes purposefully changing route patterns and traffic, slowing transmission and congesting networks. Because of this characteristic, active attacks are sometimes referred to as routing attacks. Performance is low as a result of the difficulties in identifying and mitigating these types of attacks. Worm-hole, black-hole, flooding, spoofing, and gray- hole attacks are examples of current attacks. Such protections can only be built with a thorough understanding of the dangers.
The Enhanced Energy Efficient Secure Routing (EEE-SR) protocol approach, an algorithm that identifies the lowest shortest energy path for data transmission to network nodes with secured network data communication, has been devised and applied in the proposed study attempt. This technique's greater energy efficiency boosts network throughput and network longevity. This algorithm includes energy-efficient management techniques, allowing it to make greater use of the nodes' available energy.
T-Test and Sleep and Awake Strategy Routing Algorithm
This article's unique routing approach follows the procedures involved in MANET routing operations, such as route request and route discovery. Finding the device's remaining power for picking the path from source to designation is one of the new aspects of the newly defined algorithm, and the nodes operate in two modes: sleep and awake. This will be specified by the area nodes, with one node sleeping and the others waking.
Sleep and Awake Node Selection
1. All the nodes sends a beacon signal to other nodes to receive the current location and battery power
2. Upon receiving the beacon signal other nodes shares the current location .
3. Each and every node find out the nodes within the transmission range based on the location
4. Form a cluster nodes which are in the same region .
5. Choose the head nodes which posses the high battery power in the same region
6. Head nodes define the list of sleep nodes and awake node
7. Send information to other nodes in the region and start routing process
The Algorithm's Phases
1. Have the MANET's source node send a route request RREQ to every node that contains the destination node.
2. Obtain the Route Response from the other nodes in order to communicate with the destination.
3. Determine the remaining power of each node along its path from the source to the destination.
4. Using the T-Test Procedure, approve or reject the node for route discovery.
5. Remove rejected nodes and select a new transmission path.
6. Finish the transmission's chosen path.
T-Test Methodology
The number of nodes participating in the first route discovery will be defined for n, and the total number of nodes in the MANET will be defined for N. The T-Test approach defines the Hypothesis. Selected nodes have more power than residual nodes. Rejected nodes identify which nodes have less remaining power.
Residual Power >=H0 is the True Hypothesis.
Residual Power: False Hypothesis H1
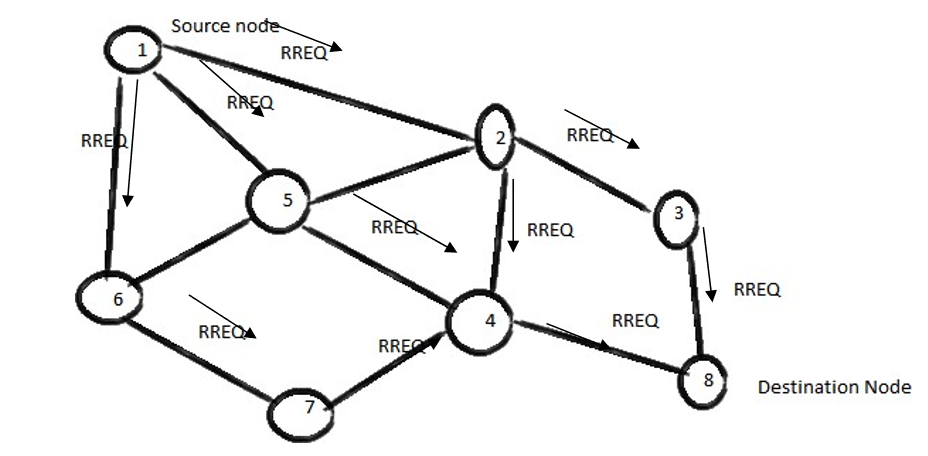
Figure 3.1: Request Route from Source to Destination Node
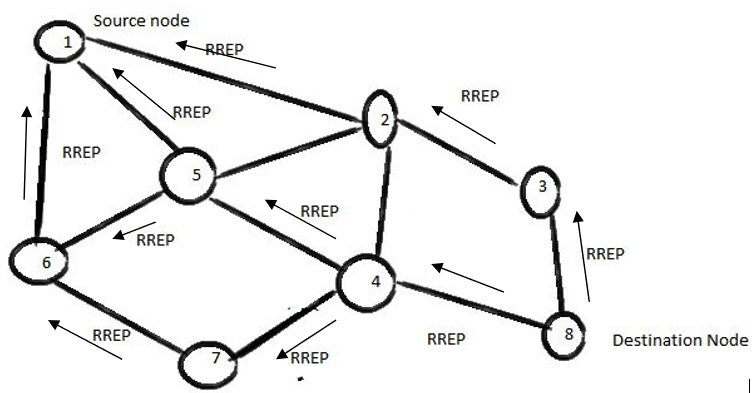
Figure 3.2: Reply Route from Destination Node to Source Node
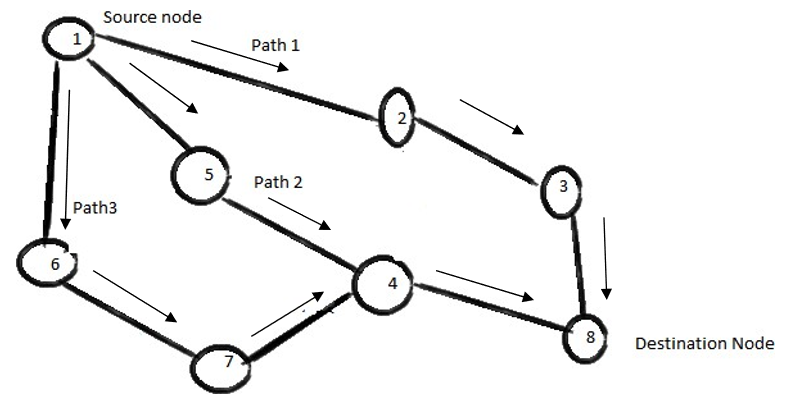
Figure 3.3: Alternative Path from Source to Destination
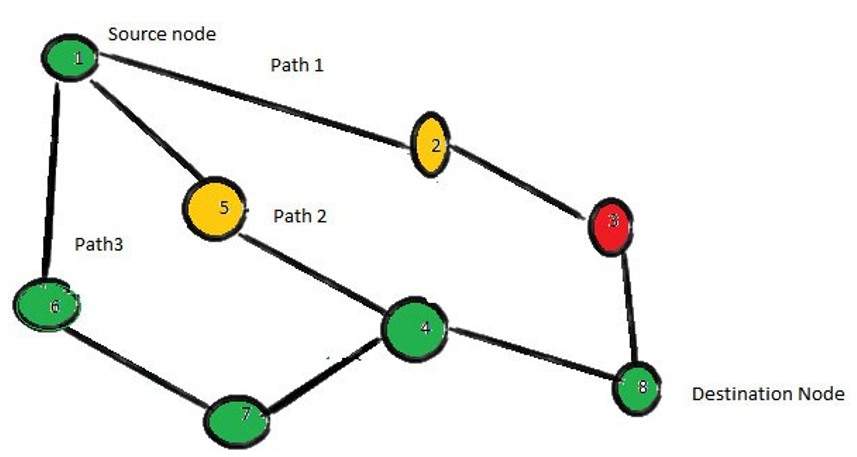
Figure 3.4: Residual Power on Two Different Paths from the Source to the Destination
The working principle of the proposed algorithm is represented in Figures 3.1 to 3.4, where a route Request is delivered from the source node to the destination node. The route reply is sent by the destination node to the source node, as shown in Figure 3.2. Figures 3.3 and 3.4 demonstrate the identification of different paths and the selection of the way that has enough energy to transport the packet, which is done by utilising the T-test process with the help of residual power availability in each node.
Simulation
The suggested routing algorithm is implemented in NS- 2 Simulator version 2.34. The simulation area is 500X 500 mm, and the number of nodes is 50, 100, and 150 with stop times of 5s, 15s, and 25 sec and average speeds of 10.10 m/s, 21.25 m/s, and 12.02 m/s, respectively. Table 1 shows the entire simulation setup for the MANET investigation.
|
Parameter Setup |
Data set |
|
Total nodes |
150, 200,250,300 |
|
Name of the source node |
5 |
|
Simulation time Set |
100s |
|
Default break time |
5s ,10s, 15s, and 25 sec |
|
speed |
11.10 m/s , 11.25 m/s and 14.02 m/s |
|
Traffic Type |
CBR |
|
Size of the Packet |
512 byte |
Table 1: Examination Simulation Setup
Table 2 displays the defined parameter value with constant bit rate traffic while estimating the Energy model for the MANET protocol performance. The omni antenna is used to determine the routing path and packet transmission. Initially, all nodes established an ideal energy of 200 joules, and other required power is also estimated and assigned, as shown in table 2.
|
Parameter |
Defined |
|
MANET Network Interface |
Wireless Physical Interface |
|
Medium Access Control type |
802.11 |
|
Type of Channel |
Wireless channel |
|
Propagation method |
TWO WAY GROUND |
|
Antenna Defined |
Omni Antenna |
|
Frequency Set |
280.8 mW (250 m) |
|
Initial node Energy |
240 Joule |
|
Rest Power |
1.5W |
|
Receiving packet Power |
1.0W |
|
Transmission packet Power |
1.5w |
Table 2: Energy Model Parameter Specifications
Result and Discussion
The suggested routing algorithm is compared to the existing AODV protocol since the AODV is an on-demand protocol that supports defining the optimum path between source and destination.
To locate the route discovery, the source node sends the Route Request to all nodes and waits for the router response. Figure 5.1 shows a comparison of route request and route reply with the existing AODV Protocol.
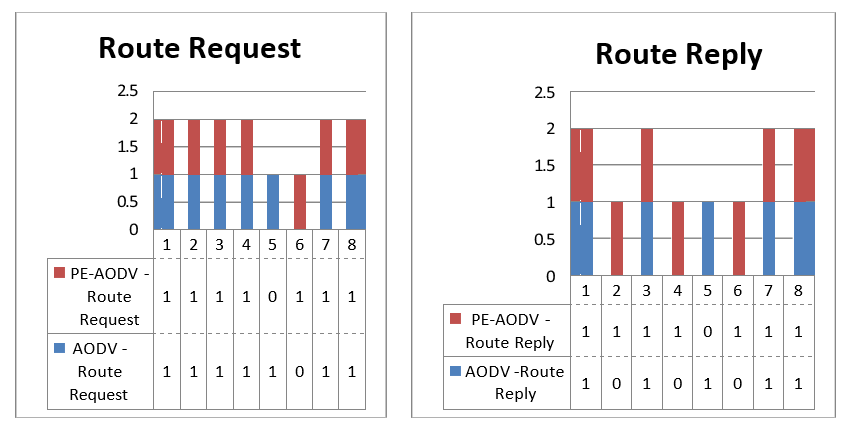
Figure 5.1: Request for Route
Route Exploration
At this step, the suggested approach is critical for selecting the most power-efficient node for packet transmission.Using the T Test Procedure, each node's residual power is evaluated, and the node path with the most energy is chosen. The comparison for taking the time to select the optimum path is made with the AODV protocol, which indicates a little delay in path selection in the PE AODV protocol. This delay is manageable and has no effect on the MANET's performance, as demonstrated in Figure 5.2. Finally, the protocol performance parameters are summarised in Figure 5.3.
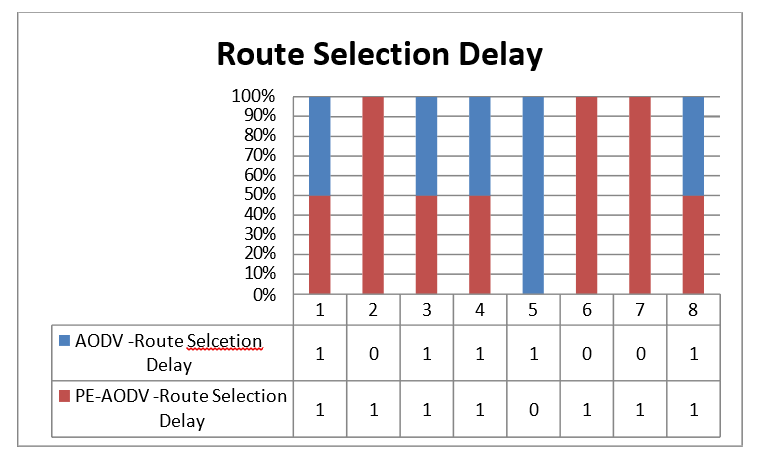
Figure 5.2: Route selection Delay
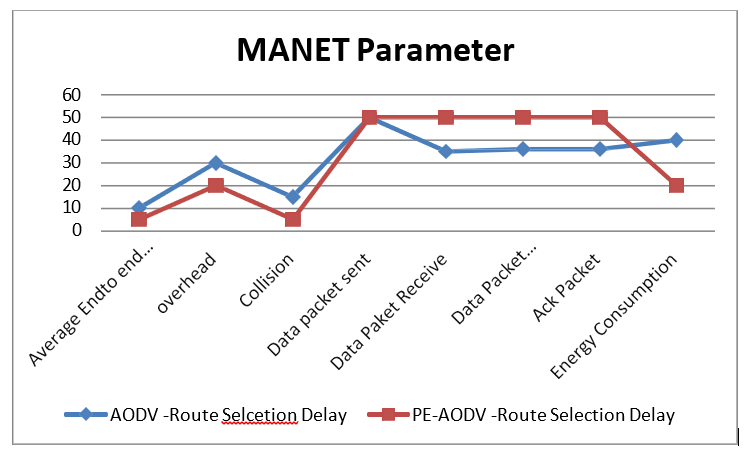
Figure 5.3: Parameter Comparisons
Conclusion
The Routing Algorithm for Efficient Packet Transmission in MANET Using T -Test Procedure is constructed with the help of a Network Simulator, and the results were compared with the current protocol, which showed that it performed better than the other MANET protocols. The T-Test is crucial in determining the best path along the trip.This protocol could be incorporated as a feature in the Making new protocol stack for the MANET network layer route finding.
References
- V.K. Quy, N.T. Ban, B.D. Tho, N.D. Han, Performance analysis of MANET employing AODV, DSR, OLSR and DSDV Routing Protocols, in: Proc. Conf. on Fundamental and Applied Information Technology Research (FAIR’8), Hanoi, 2018, pp. 96–102.
- XIONG, J., ZHAO, J., & XUAN, L. (2013). RESEARCH ON THE COMBINING OF COMPRESSED SENSING AND NETWORK CODING IN WIRELESS SENSORNETWORK. Journal of Theoretical & Applied Information Technology, 47(3).
- Krishnamachari, L., Estrin, D., & Wicker, S. (2002, July). The impact of data aggregation in wireless sensor networks. In Proceedings 22nd international conference on distributed computing systems workshops (pp. 575-578). IEEE.
- Nakamura, E. F., Ramos, H. S., Villas, L. A., de Oliveira, H. A., de Aquino, A. L., & Loureiro, A. A. (2009). A reactive role assignment for data routing in event-based wireless sensor networks. Computer Networks, 53(12), 1980-1996.
- Kuo, W. K., & Chu, S. H. (2016). Energy efficiency optimization for mobile ad hoc networks. IEEE Access, 4, 928-940.
- Prasad, R., & Shivashankar, D. (2020). Energy Secured Intrusion Detection System and Analysis of Attacks for Mobile Ad-Hoc Networks. J. Commun., 15(5), 406-414.
- Shankar, S., Varaprasad, G., & Suresh, H. N. (2014). Importance of onâ?demand modified power aware dynamic source routing protocol in mobile adâ?hoc networks. IETMicrowaves, Antennas & Propagation, 8(7), 459-464.
- Hu, Y. C., Perrig, A., & Johnson, D. B. (2002, September). Ariadne: A secure on-demand routing protocol for ad hoc networks. In Proceedings of the 8th annual international conference on Mobile computing and networking (pp. 12- 23).
- Gupta, A. K., Sadawarti, H., & Verma, A. K. (2011). A review of routing protocols for mobile ad hoc networks. WSEAS Transactions on communications, 10(11), 331-340.
- Ruta, M., Zacheo, G., Grieco, L. A., Di Noia, T., Boggia, G., Tinelli, E., ... & Di Sciascio, E. (2010). Semantic-based resource discovery, composition and substitution in IEEE802.11 mobile ad hoc networks. Wireless Networks, 16, 1223-1251.
- Tamilarasi, M., Chandramathi, S., & Palanivelu, T. G. (2001). Efficient energy management for mobile ad hoc networks. Ubiquitous Computing and Communication Journal, 3(5), 12-19.
- Prabha, R., & Ramaraj, N. (2015). An improved multipath MANET routing using link estimation and swarm intelligence. EURASIP Journal on Wireless Communications and Networking, 2015, 1.
- Thaseen, I. S., & Santhi, K. (2012). Performance analysis of FSR, LAR and ZRP routing protocols in MANET. International Journal of Computer Applications, 41(4).
- Olariu, S., Xu, Q., & Zomaya, A. Y. (2004, December). An energy-efficient self-organization protocol for wireless sensor networks. In Proceedings of the 2004 Intelligent Sensors, Sensor Networks and Information Processing Conference, 2004. (pp. 55-60). IEEE.
- Xu, G., Borcea, C., & Iftode, L. (2010). A policy enforcing mechanism for trusted ad hoc networks. IEEE Transactions on Dependable and Secure Computing, 8(3), 321-336.