Research Article - (2024) Volume 1, Issue 1
Implementation of A Smart System for Combating Human Kidnapping
2Department of Software Engineering Federal University of Technology, Akure, Nigeria
Received Date: Jul 31, 2024 / Accepted Date: Sep 05, 2024 / Published Date: Oct 01, 2024
Copyright: ©©2024 Oluwole Charles Akinyokun, et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Citation: Akinyokun. O. C., Omoruyi. O. K. (2024). Implementation of A Smart System for Combating Human Kidnapping. J of App Eng Education, 1(1), 01-15.
Abstract
The paper presents the implementation of a system for combating human kidnapping using smart objects and Internet of things. The implementation contains the technical details of the hardware and software requirements, the mapping of the experimental testbed, implementation procedure and user interface of the application. The case study of kidnapped victims between Ibadan, Oyo State and Ilishan Remo, Ogun State in Nigeria was carried out to test the adequacy and practical functions of the application. The evaluation and comparative analysis of the system on the basis of coverage area, cost incurred in deployment, positioning accuracy and signal sensitivity is carried out and the result obtained presented.
Introduction
The literature review of existing studies carried out on combating human kidnapping using smart objects and Internet of things has been presented in Akinyokun et al, 2022 and Omoruyi, 2023. The architecture of the Smart system for combating human kidnapping has been presented in Akinyokun and Omoruyi, 2023. The implementation of Smart system contains the technical details of the hardware and software requirements, the mapping of the experimental testbed, implementation procedures and user interfaces of the application. A case study of the application for monitoring a presumed kidnapped victim between Ibadan, Oyo State and Ilishan Remo, Ogun State, in Nigeria was carried out to test the adequacy and practical functions of the system. The evaluation and comparative analysis of the system is based on coverage area, cost incurred in deployment, positioning accuracy and signal sensitivity.
Implementation Procedure
The implementation procedure is comprised of:
• System hardware and software requirements.
• Experimental test-bed setup.
• Case study of simulated victim.
• Object recognition and identification module.
System Hardware and Software Requirements
The technical details, specification and functional requirements of the hardware and software used stated as follows:
• Hardware Requirements
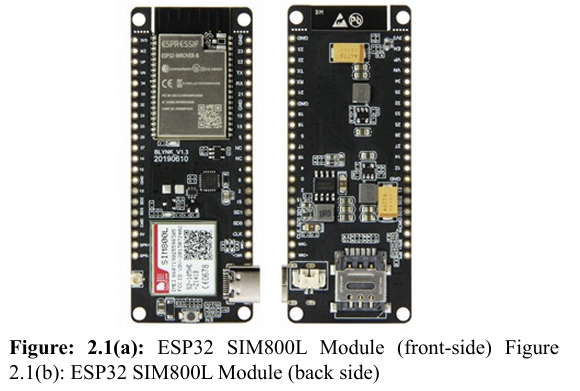
The hardware requirements are GPS modules, GSM modules, RFID tags, antennas and readers, IP cameras, Arduino-based microcontrollers, Raspberry Pi and cloud servers. The research utilised ESP32 SIM800L T-call GPRS Microcontroller and NEO 6M GPS modules for the GPS tracking. The components are shown in Figure A combination of these two modules allows for a seamless tracking of an object at any location and at any time if it is within the signal coverage of the underlying GSM network. The ESP32 SIM800L T-Call GPRS features very low power consumption when in sleep mode especially when integrated with batteries having a long standby time. The NEO 6m GPS has reliable signal reception sensitivity. The module is controlled by AT commands via UART and supports both 3.3V and 5V logic level. The ESP32 SIM800L offers the advantage of portability. These are depicted in Figures 2.1(a), 2.1(b) and 2.1(c).

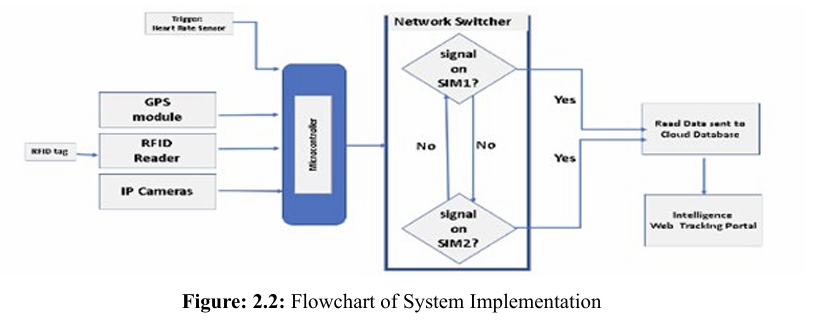
A critical block shown in Figure 2.2 is the Network Switcher which consists of two GSM module, one serving as the primary medium for Internet connection and the other serving as backup. The Network Switcher ensures that on occasions where there is no network on the primary GSM module, signal reception is switched to the secondary GSM module with a different SIM carrier provid er. This arrangement is aimed at reducing blind spots as much as possible and improves the chances of always knowing the where abouts of the victim.
The complementary RFID tracking subsystem made use of wearable RFID tags, antennas and readers strategically stationed in designated landmarks. The RFID sub-system also supports multi-detection of tags and offers a high baud rate that ranges from 2400 bps to 19200 bps. The chosen RFID reader used in the implementation has a tag read range of 10 Metres. It is equipped with an antenna to extend the signal coverage. These are depicted in Figures 2.3(a), 2.3(b) and 2.3(c). 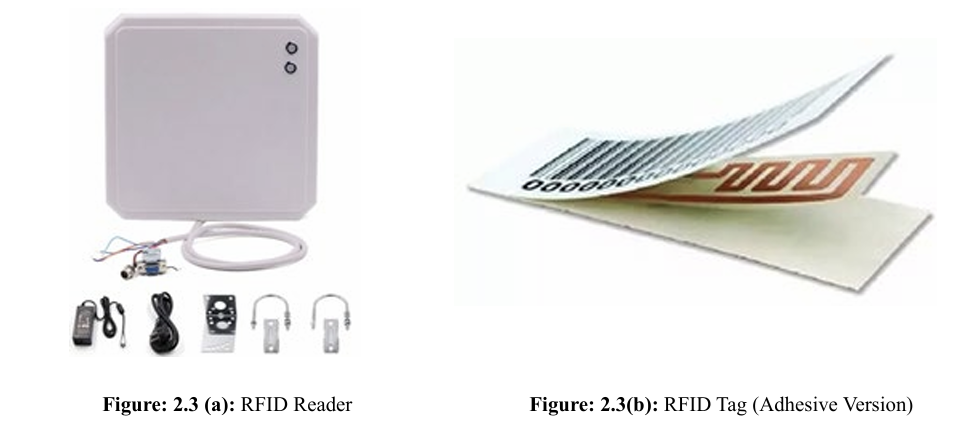

Table 2.1 and Figure 2.4 shows the RFID reading distance with the tag no barrier and obstructed by various barriers. 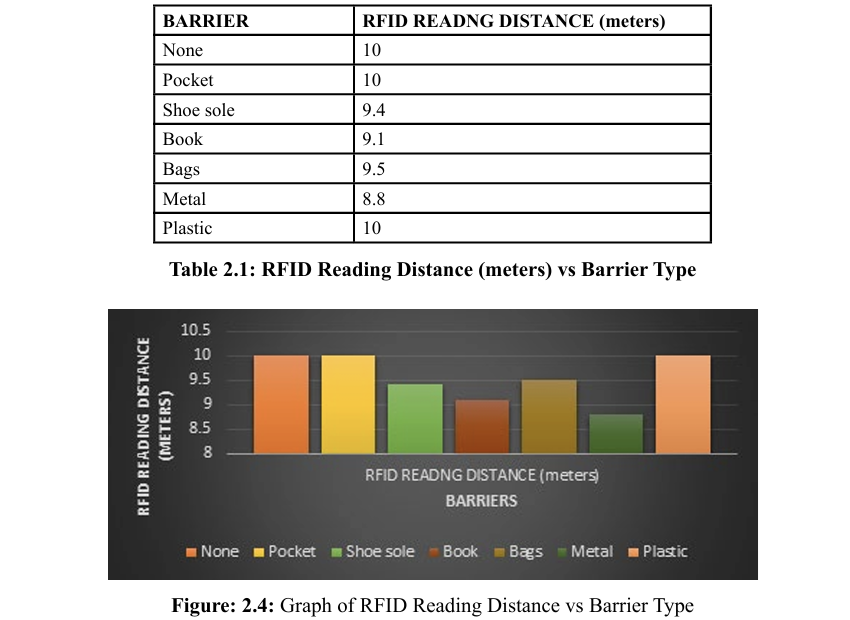
• Software Requirements
The system is developed using Python (version 3.11.4), PHP (version 8.2) and JavaScript (ECMAScript ES6) programming languages, MySQL (version 8.0) database management system, XAMPP as the local server and Google Map API as the mapping and geo-coding platform. Recognition AWS Cloud services and YOLOv8 (You-Only-Look-Once) algorithm are also utilised in the development of the Facial recognition and identification module of the system. Experimental Test-Bed Setup The research was conducted on the Housing Estate at NorthGate, Sasa, Ojoo, Federal School of Statistics zone, Ibadan, Oyo State, Nigeria. It is in the Southern part of Oyo State. The aerial view of the housing estate landscape is shown in Figure 2.5. It is lo cated within the following satellite coordinates (7.477847) and (3.907565) to the north of the estate and (7.478070) and (3.908681) to the south of the estate. The position tracking of an assumed kid napped victim was used as a case study for the research. 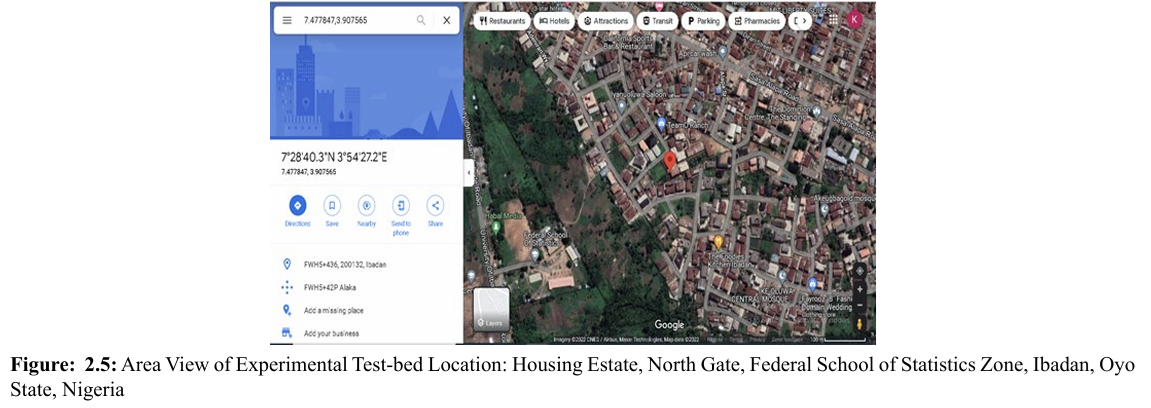
Figure 2.5 was captured using Google Maps platform. The coordinate of the area was utilized in the geolocating. The red marker on the centre of the map indicates the current position of the simulated assumed victim. The application is activated by clicking on a web browser and entering the web address of the application in the address bar, which will take the user to the home page as depicted in Figure 2.6.
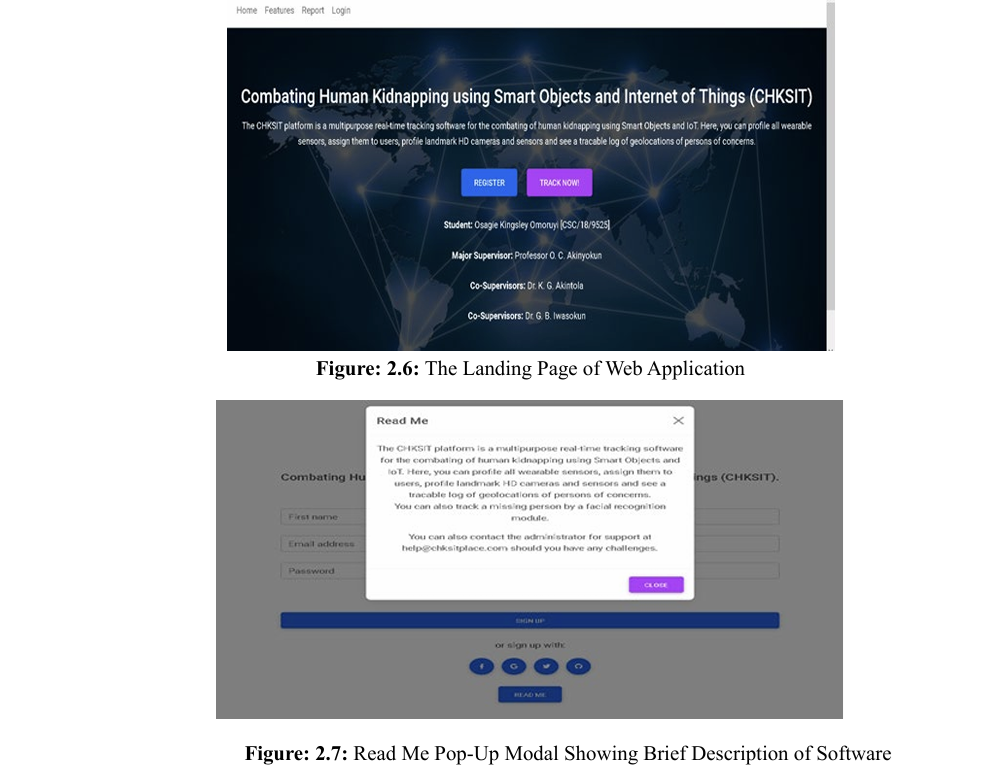
When the “Read Me” button is clicked, it opens the page showing a brief description of the system as shown in Figure 2.7. The user is taken to the login page when he or she clicks on the “Login” button. On this page, the user registers as the System Administrator to use the system for the first time as shown in Figure 2.8. 
On successful registration, the user is expected to sign into the system through the view shown in Figure 2.8. There is a “Password Reminder” module to assist the users in cases where they cannot recall their correct username or password. On successful login, the user is taken to the configuration page, where the following entities can be set up:
• Profile
• Mobile Electronic Devices
• Immobile Electronic Devices
• Landmarks
• Geo-locations
After a successful configuration of the system, an enrolled user can be tracked anywhere in the world if he or she is putting on the wearable device. Due to the unpredictability of location in kidnapping cases, no perimeter restriction is set up on the system. This is to enable the possibility of a missing victim to be tracked from any location. Case Study of Simulated Victim An RFID reader and IP camera were installed at strategic locations and landmarks. The RFID reader scans and monitors the environment to read tags within its range that have been registered on the database. Similarly, the IP camera, which is linked with a pre-trained facial recognition and identification model monitors the environment to compare the faces within its field coverage to faces on the database that has been flagged for surveillance search. The RFID reader serves as a fail-safe alternative to the GPS receiver which is battery operated and renowned for making it impossible to track when the battery drains out. When this is the case, any closest long-range RFID reader can pick up a signal from the wearable RFID tag on the victim’s dress accessories and trigger a notification message to the server room or web portal.
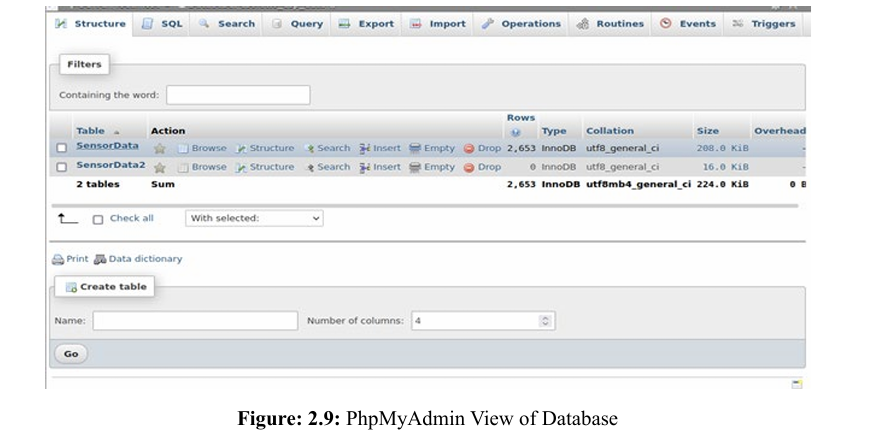
Figure 2.9 shows the GPS recording sent to the remote database server during the period of the simulated kidnapping scenario. A total of 2,653 records consisting of the longitude and latitude coordinates was captured during the tracking period from Ibadan, Oyo State to Ilisan Remo, Ogun State. 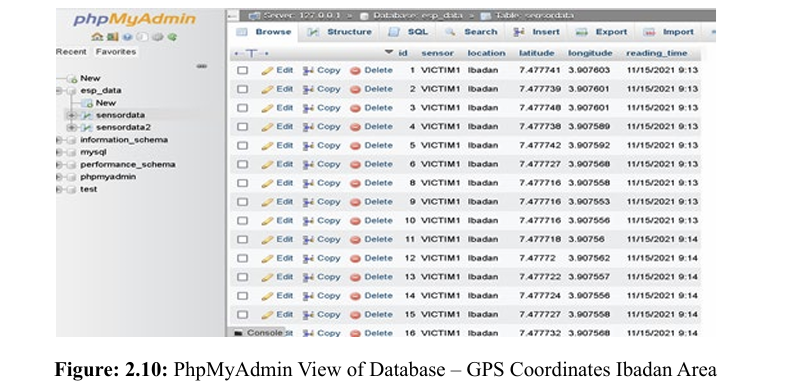
Figure 2.10 shows a subset of the GPS coordinate recording covering the Ibadan, Oyo State axis of the simulated route for this experiment. 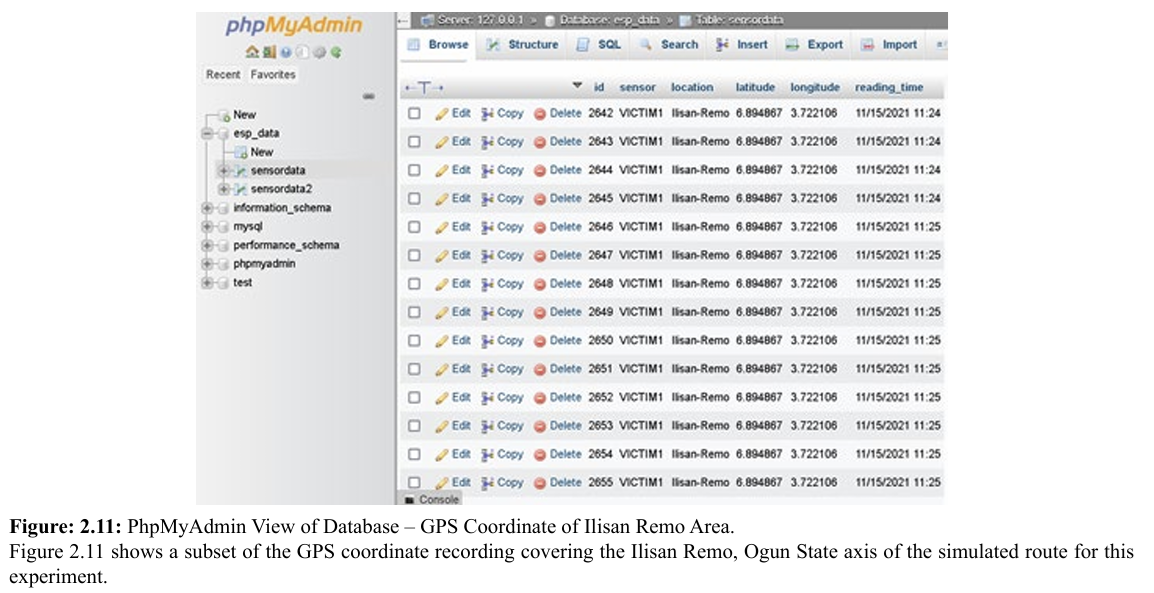
The captured data stream was connected to the latest edition of Google Earth Pro, version 7.3 to view and monitor the progression of the movement of the kidnapped victim. 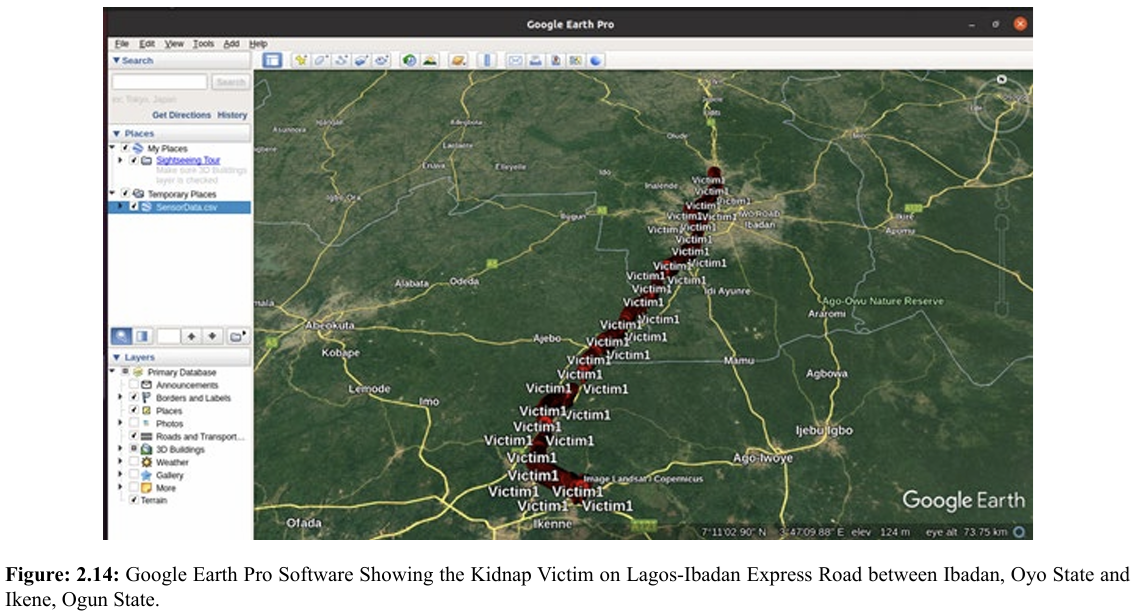 Figure 2.14 shows the timeline of the victim’s movement. It is depicted with a dynamic red marker on the map. The plot was generated at a rate of one record per second, hence the crowded marker of the victim’s location on the map. This was done to make sure we can track the location of the victim in near real time as much as possible, specifically per seconds in this instance. On Figure 1.15, the map plot rate was set at a record per minute, hence an enhanced timeline was achieved.
Figure 2.14 shows the timeline of the victim’s movement. It is depicted with a dynamic red marker on the map. The plot was generated at a rate of one record per second, hence the crowded marker of the victim’s location on the map. This was done to make sure we can track the location of the victim in near real time as much as possible, specifically per seconds in this instance. On Figure 1.15, the map plot rate was set at a record per minute, hence an enhanced timeline was achieved. 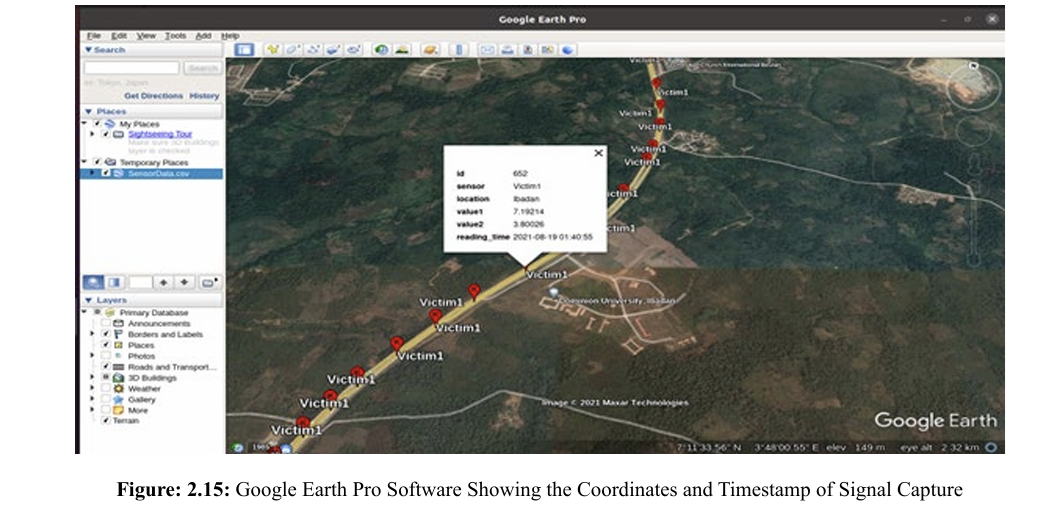
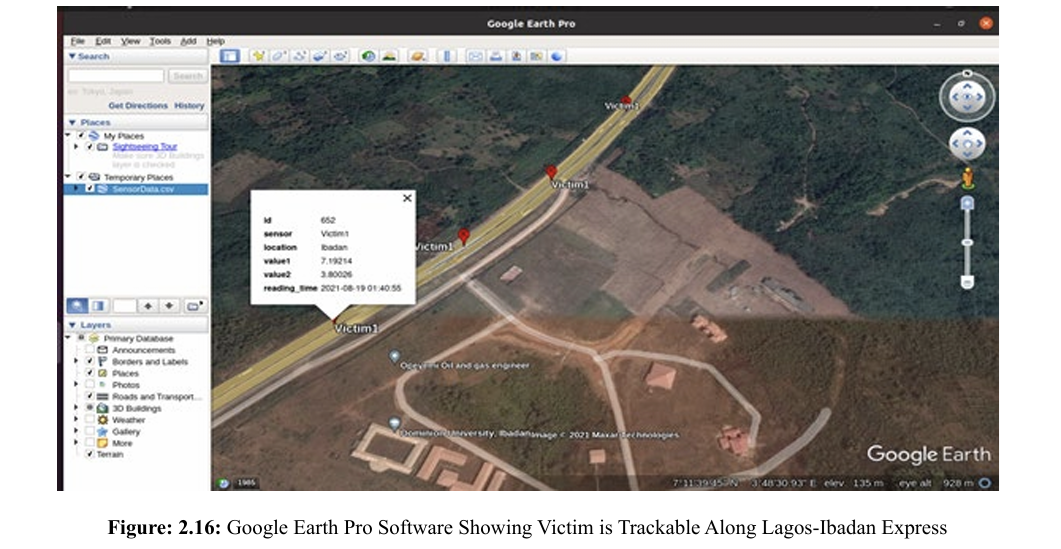
On Figures 2.16 and 2.17, an info tip marker was generated for each point. This is useful in a worst-case scenario when the wearable GPS receiver has run out of power supply due to a drained battery. The platform provides in addition to historical coordinates, the timestamp of any point of interest. 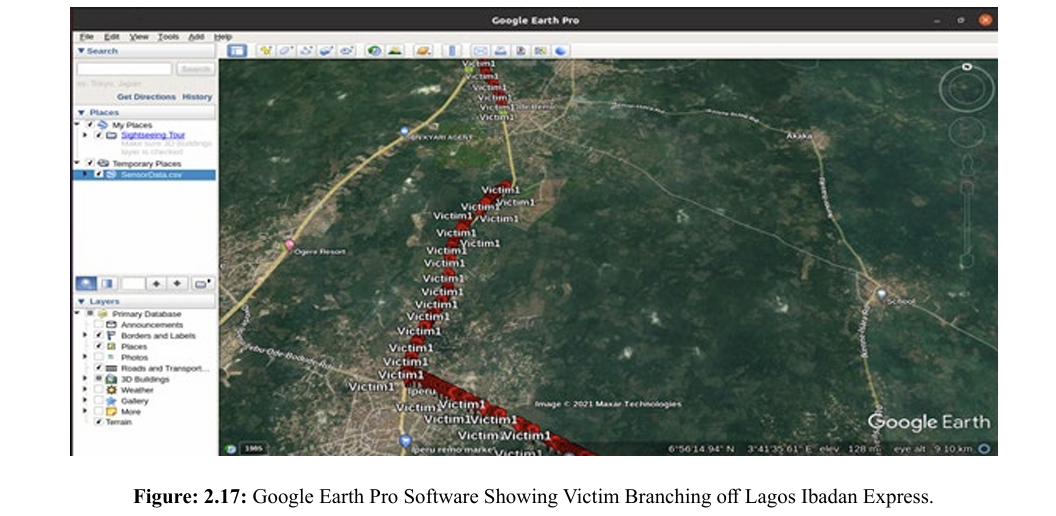
2.18 shows a no-signal zone between two close cities, Ode Remo and Ilishan Remo in Ogun State. This is a potential landmark for RFID Reader installation to serve as a fail-safe alternative. 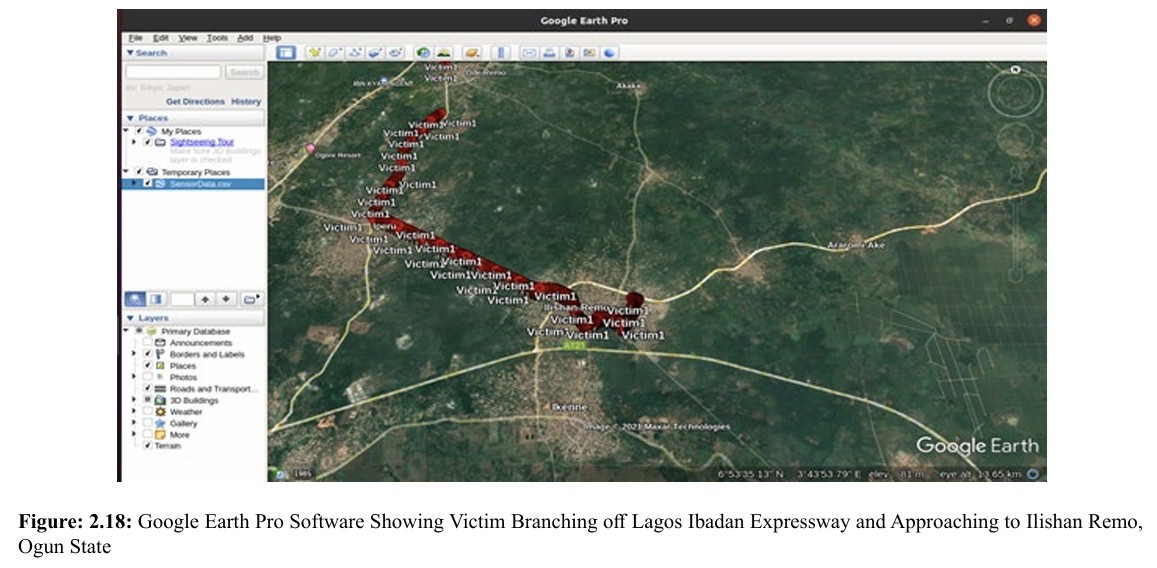
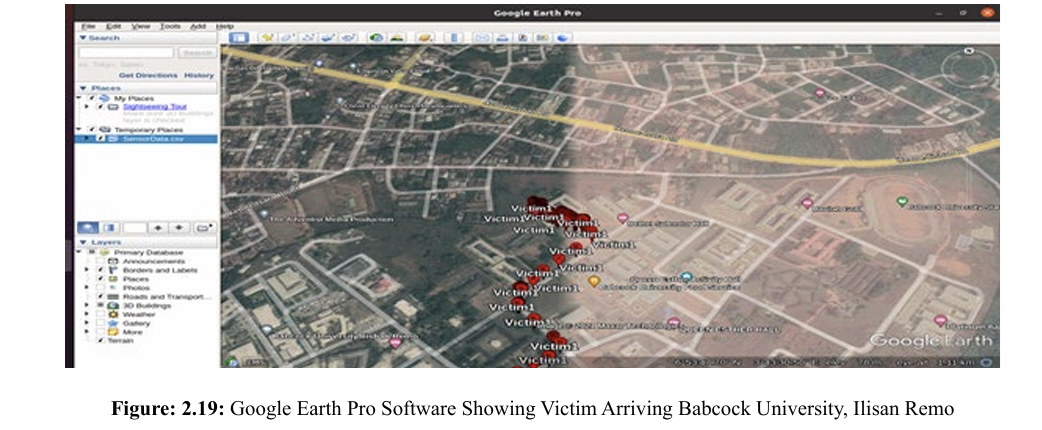
Figures 2.18 and 2.19 show the crowded position markers depicting the slow movement of the victim as the course has moved off the expressway to an intra-city road. The end of the tracking terminates at Bethel Splendor Male Hall at Babcock University, Ilisan Remo, Ogun State. Object Recognition and Identification Module Two datasets were utilised in training the facial recognition and identification model. First, the Flickr-Faces-HD Dataset (FFHQ) public facial image dataset, which consists of human faces which were crawled from Flickr, was utilised. The dataset consists of 70,000 high quality PNG images at 1024 by 1024 resolution. A bespoke facial dataset was generated by taking pictures of 10 volunteers. An image recognition module was developed by training a model using 300 facial images inclusive of augmented images. The augmentation was done by skewing the images, varying the brightness, and flipping the images on its horizonal axis. This enabled us to increase the quantity of the training and testing image set. An instance of the data set is shown in Figure 2.20. Figure 2.21 shows the resultant ability of the trained model to be able to predict the age range, gender and other important features that can match a reported kidnapped victim’s features. 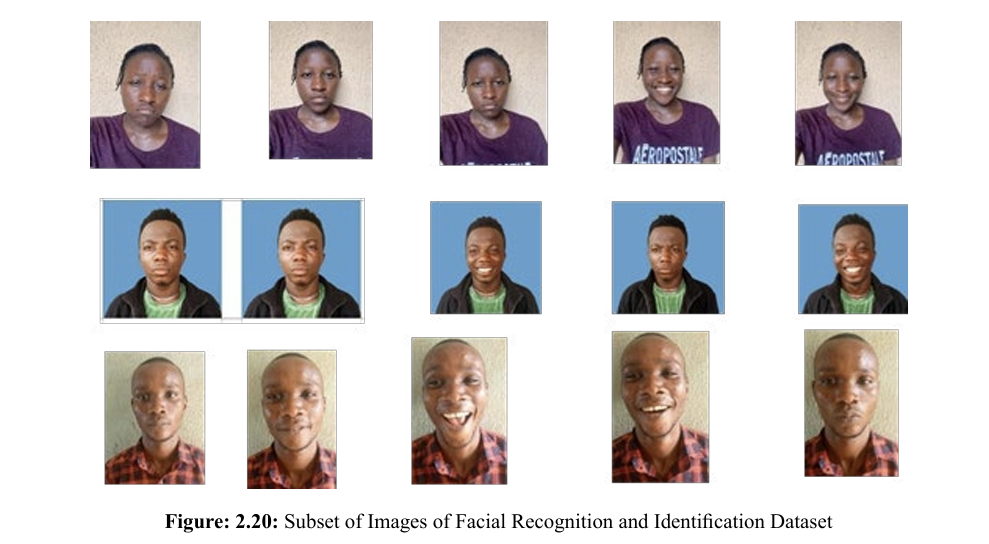
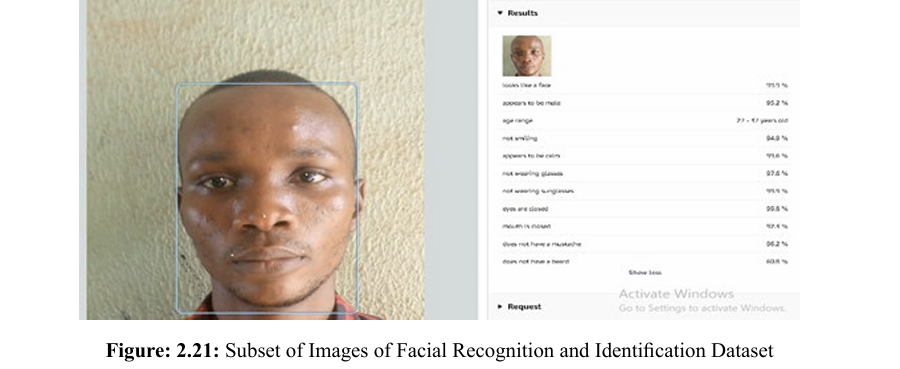
Figure: 2.22 shows the ability of the model to identify a person with a similarity score of 99.9% irrespective of the difference in facial expression. 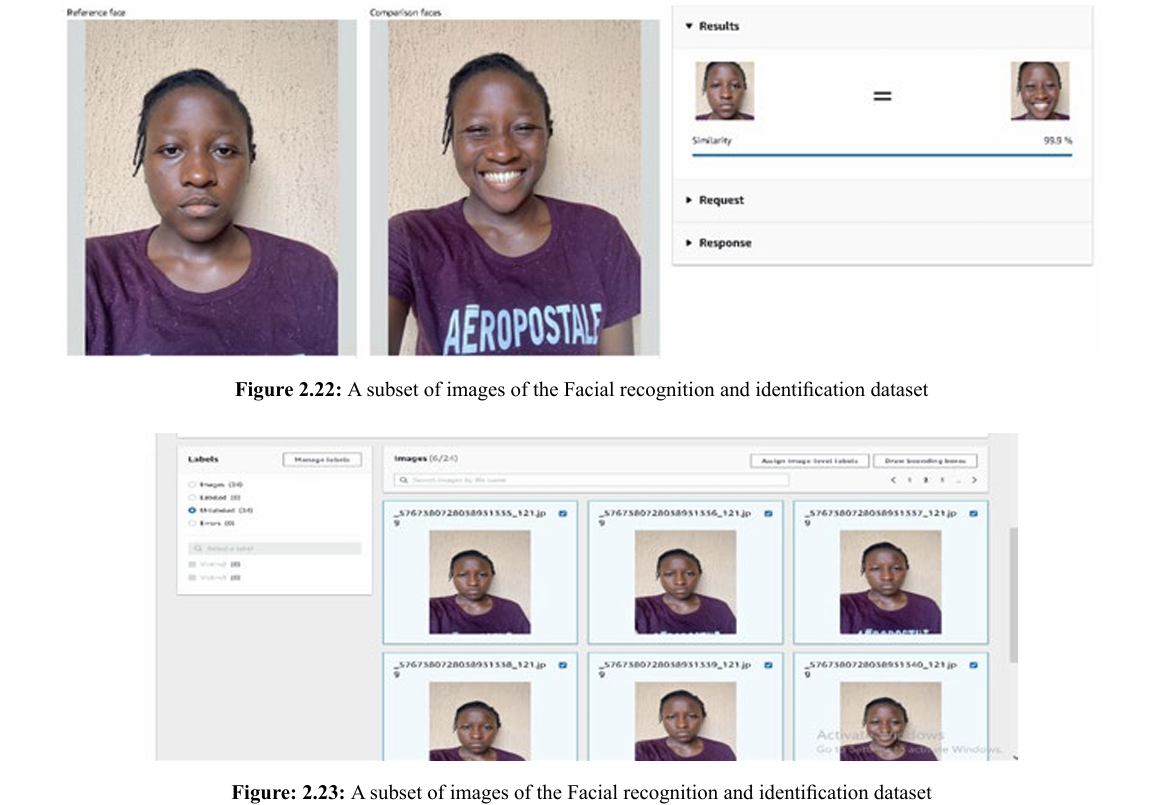
Figures 2,23 and 2.24 show the buildup of the dataset from unlabeled data to a label dataset (Victim1) respectively. The AWS ReKognition engine was used in the training. The dataset was divided into a training set and test set on an 80:20 ratio. The final model produced a recognition accuracy of above 91%.
Comparative Analysis with Existing Systems
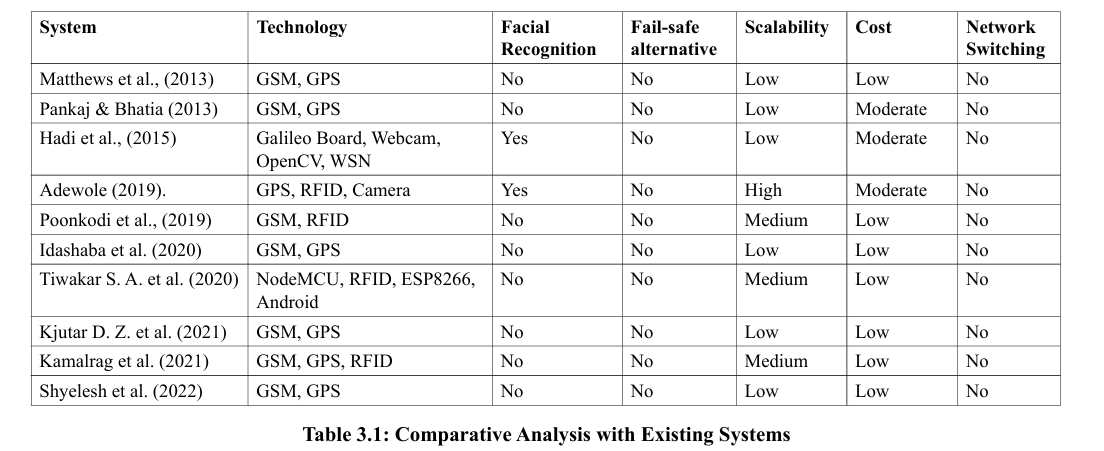
The results obtained in this research work were compared with other existing systems. The comparisons were based on the availability to a fail-safe alternative to GPS signal, victim identification, environment where they were deployed, that is, either indoor or outdoor and the metrics considered were technologies used, algorithm, accuracy, complexity, scalability, robustness and cost. Table 3.1 shows the comparative analysis of the system with other works.
Conclusion of Research Work
The primary focus of this paper is on the following:
Implementation of a smart system for combating human kidnapping using Smart Objects and Internet of Things. Carry out the case study of tracking kidnapped victim and evaluate the system and carry out the comparative analysis with other existing works. The research carried out an extensive and comprehensive review of Smart Objects and Internet of Things (IoT) and their application to solving the menace of kidnapping. Smart Objects and Internet of Things (IoT), RFID, GPS, Microcontrollers, GSM module, Smart cameras were used in the research. A web application portal was developed for easy profiling of devices, victims, landmarks and real-time tracking of object and object recognition with a view to improving the security awareness of a community and providing data for informative investigation and efficient tracking of kidnapped victims. The study successfully tracks, in real-time victims wearing a covert GPS device and recognizes simulated victims at landmarks using object recognition technology at 90% accuracy. RFID has been used to implement fail-safe alternatives in areas where there is no signal or weak GPS signal or there is loss of power on the GPS device. The research established a system for combating human kidnapping harnessing the features of Smart Objects and Internet of Things. Development of a hybrid Smart Objects and IoT-based system with fail-safe alternative that increases the availability and accuracy of the localization data sent to the cloud service and foster facial identification of kidnappers and victims.
The testbed area spans between Ibadan and Ogun State, hence more landscape or inter-state road network needs to be covered. Due to the nature of the express road networks, the effects of signal diffraction usually associated with high rise buildings and skyscrapers could not be investigated. The application developed in this research is a Web Application. The development of a mobile version of the system will ensure its mobility and seamless real time monitoring of persons. For budgetary constraints, only two volunteers could be accommodated. Experiment on larger number of volunteers is recommended. Integration of the system with existing National database like the National Identity Management Commission (NIMC) portal is suggested for further study. A further look into nanotechnology can be carried out to improve the miniaturization of devices.
References
1. Graham, I, (2005). Kidnapping by Country: Definition, Graph and Map. Retrieved 26th May, 2014 from http://www.nation master.com
2. Kortuem, G., Kawsar, F., Sundramoorthy, V., & Fitton, D. (2009). Smart objects as building blocks for the internet of things. IEEE internet computing, 14(1), 44-51.
3. Kosmatos, E. A., Tselikas, N. D., & Boucouvalas, A. C. (2011). Integrating RFIDs and smart objects into a UnifiedInternet of Things architecture. Advances in Internet of Things, 1(1), 5-12.
4. Rozyyev, A., Hasbullah, H., & Subhan, F. (2011). Indoor child tracking in wireless sensor network using fuzzy logic technique. Research Journal of Information Technology, 3(2), 81-92.
5. Okengwu, K. (2011). Kidnapping in Nigeria: Issues and common sense ways of surviving. Global journal of educational research, 1(1), 1-8.
6. Ning, Y., Zhong-Qin, W., Malekian, R., Ru-chuan, W., & Abdullah, A. H. (2013). Design of accurate vehicle location system using RFID. Elektronika ir Elektrotechnika, 19(8), 105-110.
7. Verma, P., & Bhatia, J. S. (2013). Design and development of GPS-GSM based tracking system with Google mapbased monitoring. International Journal of Computer Science, Engineering and Applications (IJCSEA), 3(3), 33-40.
8. Afifi, A. M. (2013). Using of Tracking systems for devices designing to face children Kidnapping Phenomenon (GSM GPRS-GPS). International Journal of Scientific and Research Publications, 3(10), 1.
9. Matthews, V. O., Adetiba E & Ike D. N. (2013). A Covert Kidnapping Alert and Location Identifier (CKALI). International Journal of Innovative Technology and Creative Engineering, Vol, 3, No. 12, Pp 1-11.
10. Atzori, L., Iera, A., & Morabito, G. (2014). From” smart objects” to” social objects”: The next evolutionary step of the internet of things. IEEE Communications Magazine, 52(1), 97-105.
11. Sungur, C., Gökgündüz, H. B., & Altun, A. A. (2014, September). Road vehicles identification and positioning system. In 2014 Federated Conference on Computer Science and Information Systems (pp. 1353-1359). IEEE.
12. Fortino, G., Guerrieri, A., Russo, W., & Savaglio, C. (2014). Middlewares for smart objects and smart environments: overview and comparison. Internet of Things based on Smart Objects: technology, middleware and applications, 1-27.
13. Uzorma, P. N., & Nwanegbo-Ben, J. O. H. N. (2014). Challenges of hostage-taking and kidnapping in the South eastern Nigeria. International Journal of Research in Humanities, Arts and Literature, 2(6), 131-142.
14. Liu, X., & Baiocchi, O. (2016, October). A comparison of the definitions for smart sensors, smart objects and Things in IoT. In 2016 IEEE 7th Annual Information Technology, Electronics and Mobile Communication Conference (IEMCON) (pp. 1-4). IEEE.
15. Patel, K. K., Patel, S. M., & Scholar, P. (2016). Internet of things-IOT: definition, characteristics, architecture, enabling technologies, application & future challenges. International journal of engineering science and computing, 6(5).
16. Chaudhari, A., Bohra, S., Karma, H., & Dhupadle, A. (2015). GPS/GSM Enabled Person Tracking System. International Journal of Inn vative Research in Science, Engineering and Technology, 4(3), 981-986.
17. Dukare S.S, Patil D. A & Rane K. P, (2015).Vehicle Tracking, Monitoring and Alerting System: A Review. Journal of Computer Applications Vol. 119, No. 10.
18. Hadi N. H. B., Saleh H. B. M. & Asi S. B. M, (2015).
19. SALEH, B. M., & ASI, S. B. M. Prevention system for child abduction by using image processing algorithm on intel Galileo board.
20. Awolusi, A.B, 2015.Development of Online System for Monitoring of Personnel in Public Service. MTech Thesis, Department of Computer Science, Federal University of Technology, Akure, Nigeria.
21. Redmon, J., Divvala, S., Girshick, R., & Farhadi, A. (2016). You only look once: Unified, real-time object detection. In Proceedings of the IEEE conference on computer vision and pattern recognition (pp. 779-788).
22. Ahmad, A., Rathore, M. M., Paul, A., Hong, W. H., & Seo, H. (2016). Contextâ?Aware Mobile Sensors for Sensing Discrete Events in Smart Environment. Journal of Sensors, 2016(1), 7283831.
23. Du, M., Jing, C., & Du, M. (2016). Tag location method integrating GNSS and RFID technology. The Journal of Global Positioning Systems, 14, 1-6.
24. Awolusi, A. B., Akinyokun, O. C., & Iwasokun, G. B. (2016). RFID and RTLS-Based Human Resource Monitoring System. J. Adv. Math. Comput. Sci, 14, 1-14.
25. Akinyokun O.C, Akintola K.G. & Olabode O, 2016 Real-Time Whole-Body Action Recognition in Videos using Threshold Hidden Markov Model. Journal of Mathematical Sciences of the National Mathematical Centre, Vol. 4, No. 1.
26. Ibrahim, B., & Mukhtar, J. I. (2016). Changing pattern of prostitution: An assessment of transnational commercial sex work by Nigerian women. European Scientific Journal, 12(2).
27. Abdulkabir, O. S. (2017). Causes and incisive solutions to the widespread of kidnapping in Nigeria current administration: Under scholastic scrutiny. Journal of Political Sciences and Public Affairs, 5(2), 23320761.
28. Gladysz, B., & Santarek, K. (2017). An approach to RTLS selection. DEStech Transactions on Engineering and Technology Research, doi, 10.
29. Akinyokun O.C, Akintola K.G & Iwasokun G.B, 2017 A Framework for Combating Human Trafficking and Kidnapping using Smart Objects and Internet-of-Things. Proceedings of the Second International Conference on Applied Information Technology (AIT 17), Abeokuta, Pp. 9-15, Nigeria.
30. Akinyokun, O. C., Kolawole, A., Babatunde, I. G., Angaye, C. O., & Arekete, S. A. (2018). Design of a framework for combating human trafficking and kidnapping using smart objects and Internet-of-things. Artif. Intell. Res., 7(1), 45-52.
31. Akinyokun, O. C., & Adewole, D. B. (2018). Monitoring of Human Resources in the Workplace. International Journal of Current Advanced Research, 7(7), 14215-14222.
32. Poonkodi R., Devaki E & Karthika M, (2019). Internet of Things Based Smart Object Tracking System. International Research Journal of Engineering and Technology, Vol. 6, No. 2, Pp. 929-932, e-ISSN: 2395-0056, p-ISSN: 2395-0072.
33. Adewole, A.B, 2019.
34. ADEWOLE, D. B. (2019). DEVELOPMENT OF A HYBRID HUMAN RESOURCES LOCATION MONITORING SYSTEM (Doctoral dissertation, FEDERAL UNIVERSITY OF TECHNOLOGY AKURE).
35. Adewole, D. B., Akinyokun, O. C., & Babatunde, I. G. (2019). Hybrid human resources localization and tracking system. Artif. Intell. Res., 8(1), 1.
36. Poonkodi, R., Devaki, E. & Karthika, M, (2019). IoT based Smart Object Tracking System. International Research Journal of Engineering and Technology, Vol. 6, No. 2, Pg. 929-932, e-ISSN: 2395-0056, p-ISSN: 2395-0072.
37. Munshi, N, (2019). Threat of Abduction Makes Nigeria a High Risk Business, Financial Times. Available in https://www. ft.com/content/99d6aaea-e394-11e9-9743-db5a370481bc
38. Adewole D. B & Akinyokun O.C, 2020Workplace and Human Resource Safety Monitoring using Internet of Things, Journal of Artificial Intelligence Research. www.sciedu.ca/air, Canada.
39. UN-CTS M5.5. United Nations Surveys on Crime Trends and the Operations of Criminal Justice Systems (UN-CTS). M5.5. Source: https://www.unodc.org/unodc/en/data-and analysis/United-Nations-Surveys-on-Crime-Trends-and-the Operations-of-Criminal-Justice-Systems.html
40. Kamalrag R. and Pooja R. (2022).RFID Child Monitoring System using IoT: A Survey. International Journal of Computational Engineering Research (IJCER). ISSN (e): 2250-3005. Vol. 12 Issue 1
41. Idachaba F. E., Odufowokan A. & Uyi Aiyudubie (2020). Development of an IoT based Smart Campus Wide Shuttle Tracking System. Proceedings of the Future Technologies Conference FTC2020. Volume 3, pp 610-621
42. Tiwarkar S. A., Bhumannavar S. S., Kshirsagar G. K. & Ghare A. D. (2020). School Child Tracker System using IoT. International Journal of Innovative Science and Research Technology. ISSN: 2456-2165, Volume 5, Issue 1
43. Shylesh S., Shahan K., Reddy Y.A.K., Naveen K. K. & Manasa K. (2022).
44. IoT Based Smart Security and Safety System for Women and Children. Journal of Emerging Technologies and Innovative Research (JETIR). Volume 9, Issue 5.
45. Khutar D. Z (2021). 46. Design and Implementation of a Smart System for School Children Tracking. IOP Conference S e r i e s : Materials Science and Engineering. doi:10.1088/1757 899X/1090/1/012033
47. Akinyokun O. C, Omoruyi O. K and Adegoke A. M, 2022. Literature Review on Positioning, Tracking and Monitoring Systems for Human Kidnapping, Journal of Trends in Technical and Science Research, Volume 5, Issue 4, www. ttsrjuniperpublishers.com, California, USA
48. Omoruyi et al., (2023)Development of a Smart System for Combating Human Kidnapping. Phd Thesis, Department of Computer Science, The Federal University of Technology, Akure, Nigeria.
49. Akinyokun O. C. and Omoruyi O. K, 2023Architecture of a Smart System for Combating Human Kidnapping. Journal of Artificial Intelligence Research. www.sciedu.ca/air, Canada.